What IT Compliance Really Means — And Why It Matters for Your Business
IT compliance is the process of ensuring your organization’s technology systems, data practices, and security controls meet the requirements set by laws, regulations, and industry standards.
Here’s a quick summary of what you need to know:
| Question | Quick Answer |
|---|---|
| What is it? | Following rules set by governments, regulators, and industry bodies for how you handle data and technology |
| Who needs it? | Nearly every business — especially in healthcare, finance, retail, and government contracting |
| Key regulations | GDPR, HIPAA, PCI DSS, SOX, NIST CSF, ISO/IEC 27001 |
| What’s at risk? | Fines, data breaches, lawsuits, and serious damage to your reputation |
| How to achieve it? | Risk assessments, security policies, employee training, audits, and automation |
Regulations keep growing. Cyber threats keep evolving. And the cost of getting it wrong keeps climbing — Meta was fined $1.3 billion in a single GDPR ruling. For business leaders and IT managers in Northeast Ohio, the pressure to stay compliant while keeping operations running smoothly is very real.
The challenge is that IT compliance isn’t a one-time checkbox. It’s an ongoing process that touches every corner of your technology environment — from how you store customer data to how you respond to a security incident.
This guide breaks it all down in plain language: what IT compliance is, which regulations apply to your business, what the consequences of non-compliance look like, and the practical steps you can take to build a program that actually works.
I’m Jay Baruffa, founder of Tech Dynamix, and with over 20 years of hands-on experience in IT infrastructure, cybersecurity, and IT compliance for businesses across Northeast Ohio, I’ve seen what happens when compliance is treated as an afterthought. This guide will help you avoid those costly mistakes and build a stronger foundation for your business.
Understanding the Core of IT Compliance

At its heart, IT compliance is about accountability. It is the practice of adhering to mandated requirements defined by laws and regulations, as well as voluntary requirements stemming from contracts and internal policies. Whether you are a manufacturing plant in Mentor or a healthcare provider in Willoughby, your business operates within a web of rules designed to protect sensitive data and ensure digital integrity.
While many people use the terms “compliance,” “security,” and “governance” interchangeably, they actually play different roles in your organization. Think of it like a three-legged stool: if one leg is missing, the whole thing topples over.
- IT Governance: This is the internal strategy. It aligns your technology with your business goals, ensuring you manage resources efficiently and measure performance.
- IT Security: This is the technical shield. It involves the tools and practices—like encryption and firewalls—that protect your data from hackers.
- IT Compliance: This is the external rulebook. It focuses on proving to third parties (like auditors or government agencies) that you are following specific standards.
To stay ahead, professionals often look to resources like Compliance in Cybersecurity: How to Stay Ahead to understand how these pieces fit together.
The Difference Between IT Security and IT Compliance
It is a common misconception that being “secure” means you are “compliant,” or vice versa. IT security is broad; it focuses on operational reliability, identifying vulnerabilities, and user education. Its goal is to stop a breach from happening.
IT compliance, on the other hand, is about meeting a specific set of requirements established by an external body. For example, you might have great security, but if you don’t have the specific documentation required by a regulator, you are non-compliant. Conversely, you could check every box on a compliance list and still get hacked if your security isn’t proactive. That’s why we emphasize comprehensive security services that go beyond the bare minimum of a checklist.
Who Needs to Comply?
If you handle data, you likely need to comply with something.
- Financial Institutions: Banks and investment firms in the Greater Cleveland Area must follow SOX and PCI DSS to protect financial integrity.
- Healthcare Providers: From large hospitals to small dental offices in Lake County, HIPAA is the law of the land for protecting patient health information (e-PHI).
- Government Contractors: If you do business with the DoD, you’ll need to navigate CMMC requirements.
- Retail Sectors: Any business in Northeast Ohio that swipes a credit card must answer to PCI DSS.
- SMBs: Even if you think you’re “too small,” laws like the CCPA or GDPR (if you have European customers) can apply to you.
Major Regulations and Frameworks
Navigating the alphabet soup of regulations can be dizzying. Here are the heavy hitters that most businesses in our region encounter:
- GDPR (General Data Protection Regulation): One of the world’s strictest privacy laws. If you process data for residents in the European Economic Area, you must comply. It demands “data protection by design and by default.” You can find the Official GDPR requirements online for a deep dive.
- HIPAA (Health Insurance Portability and Accountability Act): This requires “covered entities” to ensure the confidentiality and availability of electronic health data. The HIPAA Privacy and Security Rules outline exactly how to safeguard patient info.
- PCI DSS (Payment Card Industry Data Security Standard): A set of 12 standards with over 281 guidelines for anyone handling credit cards.
- SOX (Sarbanes-Oxley Act): Aimed at public companies to prevent accounting scandals, it requires strict IT compliance regarding financial reporting.
- NIST CSF (National Institute of Standards and Technology Cybersecurity Framework): A voluntary framework that helps organizations of all sizes identify, protect, detect, respond to, and recover from cyber threats.
Global and Industry Standards
Beyond the big names, there are several other frameworks that provide a roadmap for excellence:
- ISO/IEC 27001: An international standard for Information Security Management Systems (ISMS). It’s highly respected and often helps businesses meet other regulatory requirements simultaneously.
- FISMA: A federal law that requires agencies to implement information security programs.
- FedRAMP: Standardized security requirements for cloud service providers working with the federal government.
- CCPA: The California Consumer Privacy Act, which gives residents rights over their personal data—critical if your Northeast Ohio business has customers in California.
Supporting Frameworks: COBIT, NIST, and COSO
Frameworks like COBIT (Control Objectives for Information Technology) help bridge the gap between business risks and technical requirements. COSO focuses on internal controls for financial reporting, while NIST SP 800-53 provides a massive catalog of security and privacy controls for federal information systems. These aren’t just “extra work”—they are the blueprints that help us build a process-oriented approach to technology.
Building an Effective IT Compliance Program
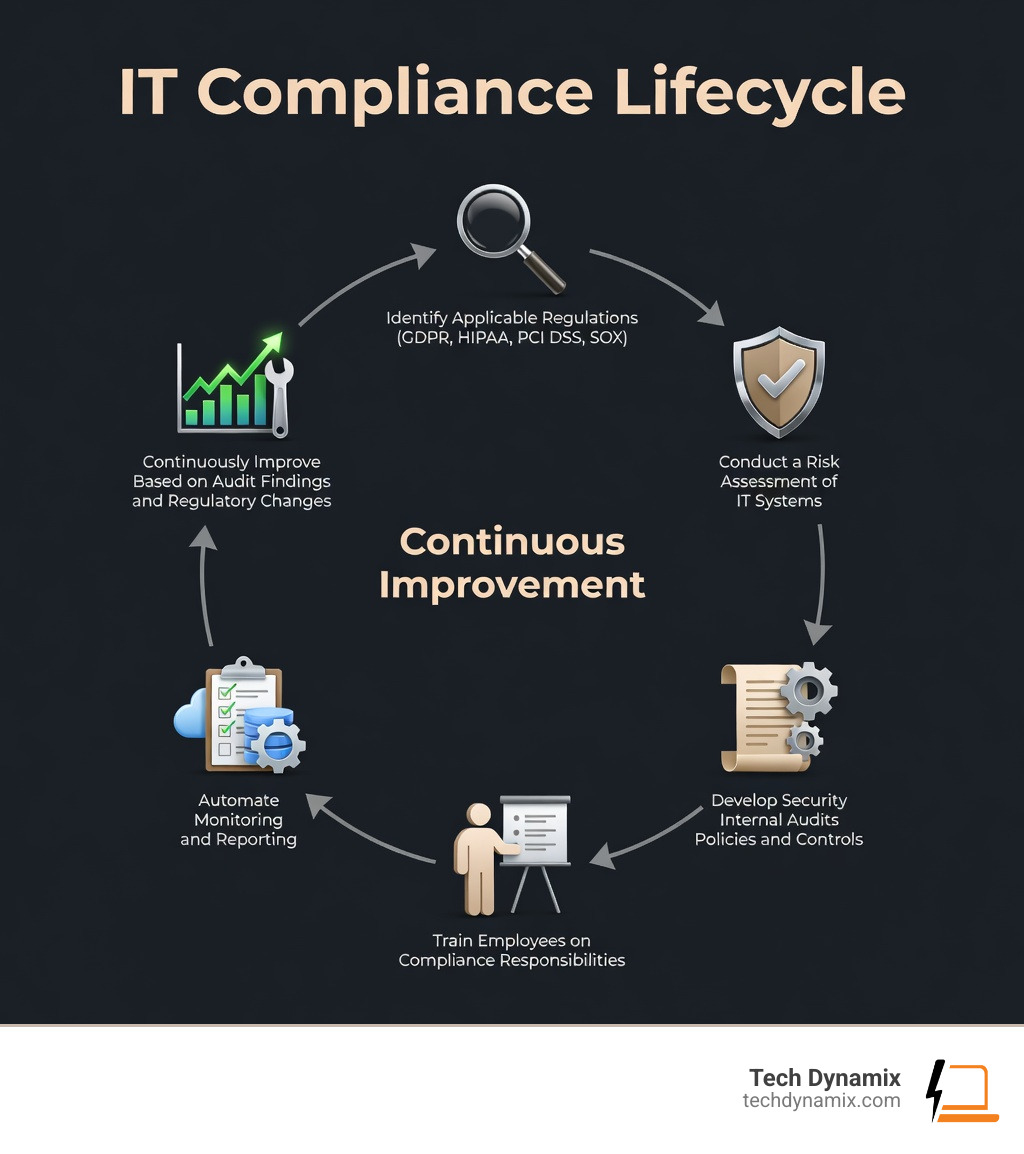
An effective program isn’t built overnight. We recommend a structured approach:
- Risk Assessment: Honestly assess your environment to find where your data is and who can access it.
- Policy Development: Write clear, formal documents that communicate what is allowed and what is prohibited.
- Employee Training: Your team is your first line of defense. Regular exercises are essential.
- Continuous Monitoring: Use tools to watch your systems 24/7.
For those in the defense supply chain, we offer specialized guidance on CMMC compliance to ensure you don’t lose out on valuable contracts.
IT General Controls (ITGC) vs. IT Application Controls (ITAC)
Understanding the difference between these two types of controls is vital for passing an audit:
- IT General Controls (ITGC): These are foundational. They include change management (making sure updates don’t break things), logical access (who can log in), and disaster recovery (what happens if a server dies in Eastlake?).
- IT Application Controls (ITAC): These are specific to a software program. They ensure data is valid, authenticated, and authorized—like a system that won’t let an invoice be paid unless it matches a purchase order.
Automation in IT Compliance
Did you know that IT and security professionals spend an average of 4,300 hours a year just maintaining compliance? That is a massive drain on resources. This is why 99% of organizations are planning to move to a continuous compliance model.
Automation simplifies everything. Instead of a manual “checkbox” exercise once a year, automated tools can monitor configuration drift in real-time. By using “policy as code,” we can ensure that your systems stay compliant every single day, not just on audit day. Organizations using modern automation platforms often achieve certifications up to 90% faster and reduce audit prep efforts by 60%.
The High Cost of Non-Compliance
If you think IT compliance is expensive, try non-compliance. The financial penalties alone can be business-ending.
- Meta/Facebook: Hit with a record-breaking $1.3 billion GDPR fine in 2023.
- Anthem: Fined $16 million for a HIPAA violation that exposed 79 million members’ records.
- Equifax: Paid a $425 million settlement to the FTC following a massive data breach.
- PCI DSS Fines: These can range from $5,000 to $10,000 per month for initial non-compliance, soaring to $100,000 per month for long-term violations. You can read more about PCI DSS non-compliance fines to see just how quickly they add up.
Beyond Fines: Reputational and Operational Risks
The “hidden” costs are often worse than the fines. Target faced $292 million in cleanup costs and penalties after their 2016 breach, but they also suffered a massive erosion of customer trust. When a breach happens, you lose more than data—you lose the confidence of your partners and customers in the Cleveland Metro East Corridor. Business continuity stops, lawsuits fly, and the road to recovery is long and expensive.
Frequently Asked Questions about IT Compliance
What skills and certifications are needed for IT compliance roles?
The field is growing rapidly, with salaries ranging from $87k for entry-level roles to $145k for senior managers. Key skills include auditing, risk analysis, and strong communication. Top certifications include:
- CISA (Certified Information Systems Auditor): The gold standard for auditing.
- CompTIA Security+: A great foundational cert for understanding security controls.
- ISACA AI Governance: As AI explodes, understanding AI Governance principles is becoming a must-have skill.
How does a risk assessment reduce compliance gaps?
A risk assessment acts as a map. It helps you identify where your most sensitive data lives, what threats (like ransomware) are most likely to hit it, and where your current controls are weak. By mapping vulnerabilities to specific controls, you can reduce “residual risk” to a level that regulators—and your insurance company—can live with.
What are the first steps for an SMB to achieve compliance?
Don’t panic. Start by assessing your environment holistically. Identify which regulations actually apply to you (don’t waste time on FISMA if you aren’t a government agency!). Document your policies and start an internal audit process to see where you stand.
Conclusion
At Tech Dynamix, we understand that for small and mid-size businesses in Northeast Ohio, IT compliance can feel like an uphill battle. Whether you’re in manufacturing in Mentor or professional services in Chardon, the rules are the same, but the resources aren’t always there.
That’s where we come in. With over 20 years of local expertise, we provide proactive managed IT and cybersecurity protection that keeps you compliant without slowing you down. From Lake County to Cuyahoga County, we are your dependable all-in-one technology partner.
Ready to stop worrying about audits and start focusing on your business? Schedule a Compliance and Security Audit with us today and let’s get your systems where they need to be.