Why Auditing IT Security Policy Compliance Matters Now More Than Ever
Auditing IT security policy compliance is a systematic process that evaluates whether your organization’s IT systems, processes, and controls meet established security policies and regulatory requirements. Here’s what it involves:
Key Components of IT Security Policy Compliance Audits:
- Verify adherence to internal security policies and external regulations (GDPR, HIPAA, PCI DSS, ISO 27001)
- Identify vulnerabilities in IT infrastructure, access controls, and data protection measures
- Assess effectiveness of security controls through documentation review, interviews, and technical testing
- Recommend improvements to strengthen security posture and close compliance gaps
- Demonstrate due diligence to stakeholders, regulators, and customers
With global cybercrime costs expected to reach $10.5 trillion annually by 2025, the stakes have never been higher. A cyberattack doesn’t just compromise sensitive data—it threatens your financial position, strategic vision, and the trust you’ve built with customers over years.
Yet many Northeast Ohio businesses face a common challenge: How do you prove your security measures actually work? Regular audits aren’t just about checking boxes for compliance. They’re about identifying the gaps before attackers do, protecting client information, and avoiding the devastating consequences of data breaches.
Modern auditing has evolved. AI systems now increase threat detection accuracy from 70-80% to 90-95%, cutting detection times from weeks to hours. Organizations that adopt integrated audit approaches can leverage evidence across multiple frameworks, saving time and resources while building a more robust security strategy.
I’m Jay Baruffa, and over my 20+ years designing IT infrastructure and conducting security assessments, I’ve seen how proper auditing IT security policy compliance transforms risk management from reactive to proactive. My work with complex networks and enterprise systems across Northeast Ohio has taught me that effective audits aren’t about finding problems—they’re about building confidence in your security posture.
Understanding the Fundamentals of IT Security Audits
An IT security policy compliance audit verifies that digital defenses are actively working as intended. It establishes a security baseline, ensuring practices align with policies and regulations. For Northeast Ohio businesses, this means protecting operations from cyberattacks.
Regular security audits allow us to proactively identify security problems, gaps, and weaknesses before malicious actors can exploit them. This proactive approach is vital because the consequences of a data breach can be severe. Beyond the immediate operational disruption, data breaches can lead to significant financial penalties, legal repercussions, and long-term damage to our reputation. As we know, data breaches and security lapses can lead to lawsuits and reputational damage, making prevention far more desirable than reaction.
A key benefit of performing these audits is to demonstrate due diligence to our stakeholders, regulators, and customers. It shows that we take the security of their data seriously and are committed to maintaining a strong security posture. This builds trust, which is an invaluable asset in today’s digital economy.
We often categorize audits into two types: internal and external. An internal audit is conducted by our own team members, offering deep familiarity with our systems and processes. This allows us to identify internal weaknesses proactively and optimize our procedures. An external audit, on the other hand, is performed by an independent third-party firm. These auditors bring an unbiased, outsider’s perspective and provide assurance to external stakeholders that we are indeed compliant with regulations and industry standards. Both types play a critical role in a comprehensive security strategy, and often, a blend of both yields the best benefits.
The consequences of non-compliance with IT security policies, if identified during an audit, can range from significant fines and legal action to severe reputational damage and the loss of customer trust. For instance, a lack of adherence to specific data protection regulations could result in hefty penalties, not to mention the operational costs associated with remediating a breach. An audit helps us avoid these pitfalls by providing a clear roadmap for improvement. If you’re looking to strengthen your defenses, you can find more info about compliance & security audits on our services page.
Distinguishing Audits from Penetration Tests
While often discussed in the same breath, an IT security policy compliance audit, a general security audit, and a penetration test serve distinct purposes. Understanding these differences is crucial for effective cybersecurity planning.
A security audit, also known as a cybersecurity audit, is a comprehensive assessment of your organization’s information systems. It measures our information system’s security against an audit checklist of industry best practices, established standards, and/or federal regulations. The primary goal of an audit is to verify that our existing security controls and policies are properly implemented, effective, and compliant with relevant frameworks. It looks at the “what” and “if”—what controls do we have, and are they meeting the standards? This often involves reviewing documentation, interviewing staff, and assessing configurations to ensure adherence to our security policy.
A penetration test, or “pen test,” takes a more aggressive approach. It involves having ethical hackers attempt to attack our systems in order to uncover known vulnerabilities. Think of it as a simulated cyberattack designed to exploit weaknesses in our network, applications, or systems. The goal here is to determine how far an attacker could get into our systems and what data they could access. It focuses on the “how”—how could an attacker bypass our defenses? While an audit might identify that a firewall rule is misconfigured, a penetration test might actually exploit that misconfiguration to gain unauthorized access.
Vulnerability assessments fall somewhere in between. They identify, quantify, and rank the vulnerabilities in our systems but do not attempt to exploit them. It’s like scanning a house for open windows and doors, but not actually entering. A security audit can encompass and include both penetration tests and vulnerability assessments, but its scope is much broader, covering governance, policy adherence, and overall security posture. In short, an audit verifies compliance and control effectiveness, a vulnerability assessment identifies weaknesses, and a penetration test actively tries to break in.
Navigating Regulatory Frameworks and Policy Requirements
For businesses in Northeast Ohio, auditing IT security policy compliance isn’t just a good idea; it’s often a legal and ethical imperative. Various regulatory frameworks dictate how we must protect sensitive data, and understanding these is key to a successful audit. Each framework influences the scope and requirements of our IT security policy compliance audits.
Let’s look at some of the most prominent ones:
- GDPR (General Data Protection Regulation): While an EU regulation, GDPR impacts any organization worldwide that handles the personal data of EU residents. For our local businesses, if we have customers or employees who are EU citizens, we must comply. Audits under GDPR focus on data privacy principles, consent management, data breach notification procedures, and the lawful processing of personal data. Failing to comply can lead to significant fines. You can learn more about GDPR and data privacy.
- HIPAA (Health Insurance Portability and Accountability Act): For healthcare providers and related businesses in Ohio, HIPAA is paramount. It protects the privacy and security of sensitive patient health information (PHI). HIPAA audits scrutinize our administrative, physical, and technical safeguards to ensure PHI is protected from unauthorized access, use, or disclosure.
- PCI DSS (Payment Card Industry Data Security Standard): Any organization that processes, stores, or transmits credit card information must comply with PCI DSS. Audits here focus on network security, cardholder data protection, vulnerability management, strong access control measures, and regular security testing.
- ISO 27001 (International Organization for Standardization): This is a globally recognized standard for information security management systems (ISMS). Achieving ISO 27001 certification demonstrates that we have a systematic approach to managing sensitive company information so that it remains secure. Audits for ISO 27001 verify the implementation and effectiveness of our ISMS.
- NIST (National Institute of Standards and Technology): NIST provides widely adopted frameworks and guidelines for cybersecurity, particularly relevant for federal agencies but also widely used by the private sector. The NIST Cybersecurity Framework (CSF) helps us manage and reduce cybersecurity risks. NIST Special Publication 800-53A offers a methodology for assessing Security and Privacy Controls, providing detailed procedures for evaluating the effectiveness of our controls.
- SOX (Sarbanes-Oxley Act): Primarily focused on financial reporting accuracy for publicly traded companies, SOX has significant implications for IT controls. Our IT systems that support financial data must be secure and reliable to prevent fraud. SOX audits often examine access controls, change management, and data integrity within our IT infrastructure.
Understanding these frameworks is the first step. Our IT security policy compliance audits then tailor their scope and testing procedures to ensure we meet the specific requirements of each applicable regulation, helping us avoid penalties and build stakeholder confidence.
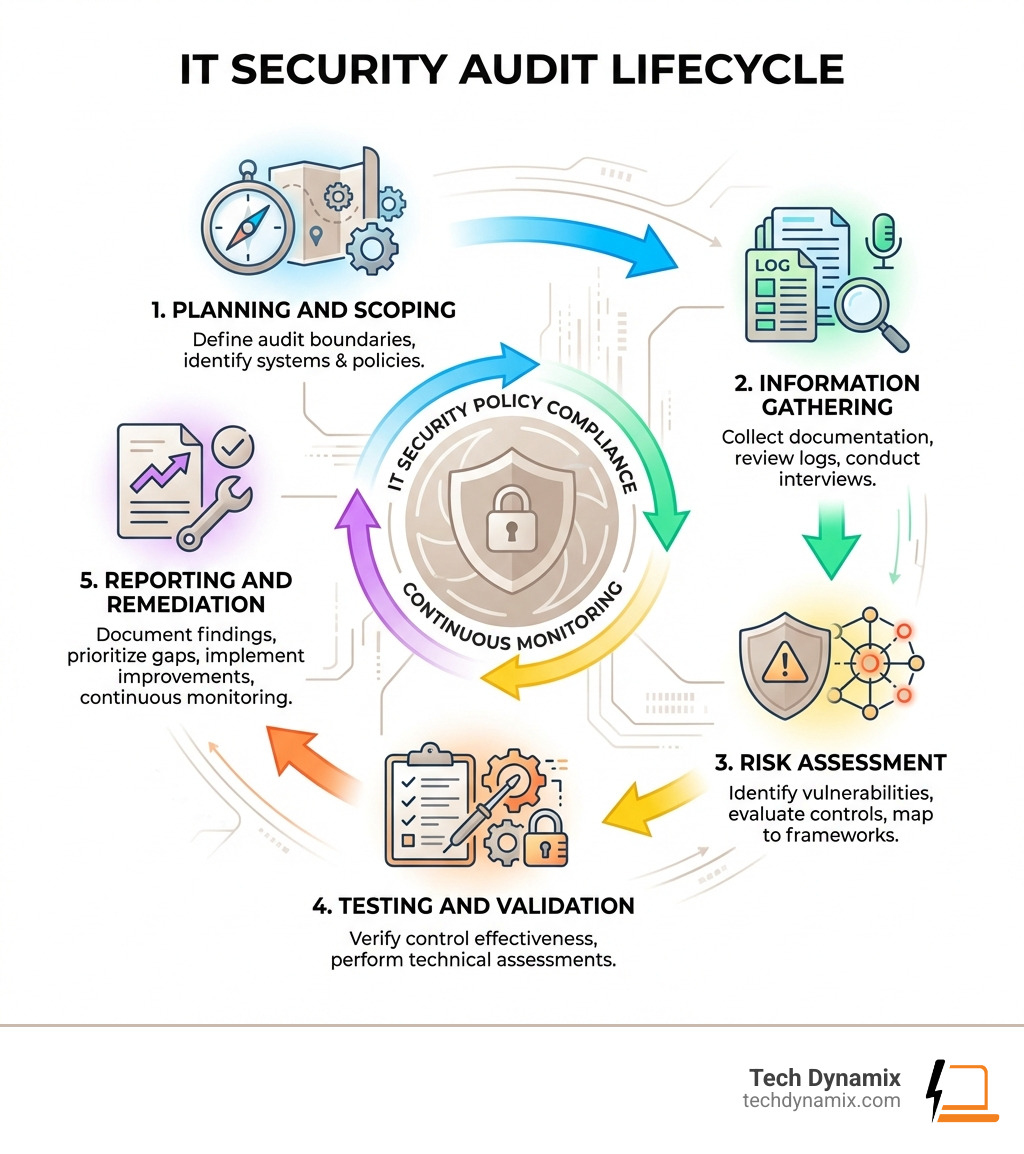
Step-by-Step Guide to Auditing IT Security Policy Compliance
Conducting an effective IT security policy compliance audit requires a structured approach. It’s not just about finding flaws; it’s about systematically verifying adherence, identifying areas for improvement, and strengthening our overall security posture.
Before diving in, let’s consider the key stakeholders and roles involved. This isn’t a one-person show; it’s a collaborative effort. Our CISO (Chief Information Security Officer) or a designated security leader typically steers the audit, providing strategic direction. The CIO (Chief Information Officer) ensures alignment with broader IT objectives. Our IT operations team, including system administrators and network engineers, provides critical technical insights and access to systems. The internal audit team offers an independent perspective, while legal and compliance teams ensure we meet all regulatory requirements. Executives and the audit committee provide oversight and resource allocation, emphasizing that a strong tone from the top is pivotal for success.
For those looking for a practical tool, a FREE DOWNLOAD › IT Compliance Audit Checklist can be an invaluable resource to get started.
Scoping for Auditing IT Security Policy Compliance
The first critical step in auditing IT security policy compliance is defining the scope. Without a clear scope, our audit can become an unwieldy and inefficient process. We need to identify precisely which systems, processes, and assets will be evaluated. This typically involves:
- Asset Inventory: We must have an up-to-date inventory of all our IT assets—servers, workstations, network devices, applications, data repositories, and cloud services. This helps us understand what needs to be protected and audited.
- Control Mapping: We’ll map our existing security controls against the requirements of the chosen regulatory frameworks (e.g., HIPAA, PCI DSS, ISO 27001). This helps us identify where our controls align and where gaps might exist. Leveraging frameworks like the NIST Cybersecurity Framework (CSF) can be particularly helpful here. NIST provides a roadmap for CSF tiers, allowing us to assess our maturity level (Partial, Risk Informed, Repeatable, Adaptive) and set targets for improvement.
- Policy Documentation Review: Our IT security policies are the backbone of compliance. We’ll review them carefully to ensure they are current, comprehensive, and clearly define acceptable use, access controls, data handling, incident response, and other critical security practices. Outdated or vague policies are an immediate red flag.
- Technical Boundaries: We need to clearly define the technical boundaries of the audit. Are we auditing only on-premise systems, cloud infrastructure, or both? Which specific applications or network segments are in scope? This clarity prevents scope creep and ensures the audit remains focused and efficient.
By carefully scoping our audit, we lay a solid foundation for a successful and impactful review of our IT security policy compliance.
Executing the Auditing IT Security Policy Compliance Process
Once the scope is defined, we move into the execution phase, where the real detective work begins. This involves gathering evidence, assessing controls, and identifying any discrepancies between our policies and our practices.
- Evidence Collection: This is a cornerstone of the audit. We gather various forms of evidence, including:
- Documentation: Security policies, procedures, configuration standards, incident response plans, and previous audit reports.
- System Logs: Reviewing logs from firewalls, intrusion detection systems, servers, and applications can reveal unauthorized access attempts, system errors, and suspicious activities.
- Configurations: Examining the configuration settings of network devices, operating systems, and applications to ensure they align with our security policies and best practices.
- Internal Risk Assessment: Before external auditors arrive, conducting an internal risk assessment allows us to proactively identify potential gaps or weaknesses in our IT controls and processes. This helps us address issues before they become findings in a formal audit.
- Employee Interviews: We’ll conduct interviews with key personnel, from IT staff to end-users and management. This helps us understand their awareness of security policies, their roles in maintaining compliance, and whether documented procedures are actually followed in practice.
- Process Assessment and Employee Shadowing: Sometimes, the best way to verify a process is to observe it firsthand. This involves shadowing employees as they perform their daily tasks, especially those involving sensitive data or critical systems, to ensure adherence to established security procedures.
- Gap Analysis: After collecting all the evidence, we perform a thorough gap analysis. This involves comparing our current state (as revealed by the evidence) against our desired state (as defined by our IT security policies and regulatory requirements). This analysis highlights areas of non-compliance, control deficiencies, and potential vulnerabilities.
Throughout this process, attention to detail is paramount. Every piece of evidence contributes to a comprehensive picture of our compliance posture, leading to actionable recommendations for improvement.
Overcoming Challenges with AI and Automation
The landscape of auditing IT security policy compliance is constantly evolving, presenting us with a unique set of challenges. Manual audit processes can be time-consuming, prone to human error, and struggle to keep pace with the sheer volume and complexity of modern IT environments-especially with the rise of cloud, hybrid, and IoT systems. Evolving regulations and a rapidly changing threat landscape, including sophisticated attacks like fileless malware and zero-day exploits, further complicate matters. These challenges are significant, especially when considering that global cybercrime costs are expected to reach $9.5 trillion a year by the end of 2024.
Fortunately, artificial intelligence (AI) and automation are revolutionizing how we approach these audits, helping us overcome these problems with remarkable efficiency and accuracy.
- Improved Performance: According to scientific research on AI-enhanced cybersecurity performance, AI-improved cybersecurity methods show higher performance metrics than traditional approaches. Threat detection speeds improve from periodic (weeks to months) to real-time (minutes to hours), and detection accuracy increases from 70-80% to 90-95% through AI-driven systems.
- Natural Language Processing (NLP): AI systems can now analyze our written security policies and documentation using NLP technology. This allows for faster and more thorough policy reviews, ensuring consistency and identifying potential ambiguities that human auditors might miss.
- Pattern Recognition and Vulnerability Prediction: AI excels at recognizing patterns in vast amounts of security data that would be impossible for humans to process. It can connect seemingly unrelated security findings to reveal hidden vulnerabilities and even predict future risks based on historical trends. This proactive capability allows us to address potential weaknesses before they are exploited.
- Automated Evidence Gathering: Automation tools can significantly streamline the collection of audit evidence, such as system logs, configurations, and access permissions. This reduces manual effort, minimizes errors, and frees up our team to focus on higher-value analysis.
- Prioritization of Issues: With AI, we can prioritize security issues based on their potential impact and likelihood, helping us allocate resources more effectively to address the most critical risks first.
By embracing AI and automation, we can transform our IT security policy compliance audits from a daunting, reactive task into a dynamic, proactive, and highly efficient process, strengthening our defenses against the ever-growing wave of cyber threats.
Best Practices for Integrated Auditing and Continuous Improvement
To ensure our auditing IT security policy compliance efforts are truly effective and efficient, we accept best practices that focus on integration and continuous improvement. It’s not a one-time event; it’s an ongoing commitment.
An integrated approach to IT and security auditing is a game-changer. Instead of treating each regulatory framework or policy in isolation, we look for overlaps and common controls. For example, many frameworks require strong access controls and data encryption. By testing these controls once, we can often generate evidence that satisfies multiple audit requirements. This approach ensures consistent communication of risk, threats, and controls across our organization, creates a common risk language, and eases the strain on our teams by allowing evidence gathered to be used across applicable frameworks. This saves valuable time and resources, which is especially important for businesses operating in today’s competitive landscape in Northeast Ohio.
A centralized data repository is crucial for this integrated approach. It provides a single source of truth where our audit and IT teams can maintain, access, and share crucial data, including policies, procedures, evidence, and remediation plans. This eliminates silos and ensures everyone is working with the most current information.
Here’s a comparison of manual versus automated audit workflows:
| Feature | Manual Audit Workflow | Automated Audit Workflow |
|---|---|---|
| Evidence Collection | Time-consuming, manual data gathering, human errors | Automated data pulls, real-time insights, reduced errors |
| Policy Review | Tedious text analysis, inconsistency risks | NLP-driven analysis, identifies gaps/inconsistencies quickly |
| Control Testing | Manual checks, limited scope, infrequent | Continuous monitoring, automated validation, broad coverage |
| Reporting | Manual compilation, static snapshots | Dynamic dashboards, customizable reports, real-time status |
| Resource Impact | High personnel effort, significant time investment | Reduced human effort, faster completion, staff reallocation |
| Accuracy | Subject to human oversight and interpretation | High consistency, objective data analysis |
| Frequency | Typically annual or semi-annual due to effort | Continuous or on-demand, enabling proactive adjustments |
Security awareness training is another non-negotiable best practice. We must educate employees on their roles and responsibilities in maintaining compliance. Promote a culture of security awareness and ensure everyone understands the importance of following established policies and procedures. A strong security posture is only as good as its weakest link, and often, that link is human error.
Finally, remediation tracking and fostering stakeholder trust go hand-in-hand. Audit findings are not failures; they are opportunities for improvement. We develop clear corrective action plans, track their implementation diligently, and communicate progress to all stakeholders. This commitment to continuous improvement, coupled with transparency, builds trust and demonstrates our unwavering dedication to protecting our information assets. Regular follow-up audits and staying informed about regulatory changes ensure that our compliance efforts remain robust and relevant.
Frequently Asked Questions about IT Security Audits
We often encounter common questions about auditing IT security policy compliance. Here, we aim to provide clear, concise answers to some of the most pressing inquiries.
What is the primary purpose of an IT security policy compliance audit?
The primary purpose of an IT security policy compliance audit is multifaceted. It’s designed to systematically evaluate whether our organization’s IT systems, processes, and controls adhere to established internal security policies, industry standards (like ISO 27001 or PCI DSS), and external regulatory requirements (such as HIPAA or GDPR). Essentially, we aim to verify compliance, identify any vulnerabilities or control deficiencies, assess the overall effectiveness of our security measures, and recommend improvements to strengthen our security posture. This process also serves to demonstrate due diligence to stakeholders, regulators, and customers, building and maintaining their trust.
How often should an organization conduct a security audit?
The frequency of security audits largely depends on several factors, including our industry, the volume and sensitivity of data we handle, our business demands, and the specific regulatory frameworks we operate under. Generally, we recommend conducting a comprehensive security audit at least once per year. However, more frequent audits may be necessary in certain situations:
- After any significant changes to our IT systems, network infrastructure, or business operations (e.g., system upgrades, data migrations, mergers, or new technology implementations).
- Following a data breach or security incident, to understand what went wrong and prevent recurrence.
- If we are subject to stringent regulations that require more frequent assessments (e.g., some levels of PCI DSS compliance may require quarterly scans).
- When the threat landscape evolves rapidly, introducing new vulnerabilities or attack vectors.
For many businesses in Northeast Ohio, a combination of annual comprehensive external audits and more frequent internal assessments (perhaps quarterly or semi-annually) provides a robust and proactive approach to maintaining compliance.
What are the consequences of failing a compliance audit?
Failing a compliance audit can have severe and far-reaching consequences for our organization. These can include:
- Financial Penalties: Many regulatory bodies impose substantial fines for non-compliance. For example, GDPR non-compliance can lead to fines of up to 4% of annual global turnover or €20 million, whichever is higher.
- Legal Repercussions: Non-compliance, especially when it leads to a data breach, can result in lawsuits from affected individuals, business partners, or regulatory bodies. This can incur significant legal fees and potential damages.
- Reputational Damage: A failed audit or a reported breach can severely damage our reputation, eroding customer trust and making it difficult to attract new clients or retain existing ones. This reputational hit can have long-term financial implications.
- Operational Disruption: Remediation efforts following a failed audit or breach can be costly and disruptive, diverting resources from core business activities. This might include system overhauls, retraining staff, and implementing new security controls.
- Loss of Certifications or Business Opportunities: For industries requiring specific certifications (like ISO 27001 or SOC 2), a failed audit can lead to the loss of these credentials, potentially impacting our ability to secure new contracts or maintain existing business relationships.
Failing a compliance audit is a clear indicator that our IT security policies and controls are not robust enough, leaving us vulnerable to cyber threats and their devastating impacts. This underscores the critical importance of regular, thorough audits and a commitment to continuous improvement.
Conclusion
In our interconnected world, auditing IT security policy compliance is a necessity for Northeast Ohio businesses. These audits serve as guardians against costly cybercrime. From distinguishing audits from penetration tests to navigating frameworks like HIPAA and GDPR, a comprehensive approach is key.
By adopting a structured guide to scoping and executing audits, and leveraging AI and automation, we can transform a daunting task into an efficient process. The best practices of integrated auditing, centralized data management, and continuous security awareness training empower us to not only meet compliance requirements but to cultivate a proactive security posture that instills confidence in our stakeholders.
The consequences of non-compliance are too severe to ignore. Instead, by embracing regular auditing IT security policy compliance, we ensure our IT environments are secure, resilient, and ready to face the challenges of tomorrow.
At Tech Dynamix, we are passionate about helping Northeast Ohio businesses achieve robust cybersecurity and compliance. Our expertise in IT consulting, cybersecurity solutions, and compliance & security audits positions us as your trusted partner. We believe in continuous monitoring and fostering a proactive security posture custom to your unique needs.
Don’t let the complexities of IT security compliance leave you vulnerable. Let us help you steer this critical landscape with confidence. Start your compliance journey with Tech Dynamix today.



