What IT Security Policy Compliance Really Means
IT security policy compliance is the process of adhering to documented rules, standards, and regulations that protect your organization’s data and technology assets. It involves implementing technical controls, training employees, and meeting legal requirements like GDPR, HIPAA, or PCI DSS to reduce cybersecurity risks and avoid costly penalties.
Quick Definition:
- What it is: A structured approach to managing cybersecurity through documented policies, procedures, and controls
- Why it matters: Protects sensitive data, meets regulatory requirements, and reduces the risk of breaches
- Key components: Access controls, encryption standards, incident response plans, and employee training
- Common frameworks: NIST Cybersecurity Framework, ISO 27001, SOC 2, and industry-specific regulations
If you’re a business leader or IT manager in Northeast Ohio, you’ve probably asked yourself: “What are we doing to make sure we’re not the next ransomware victim?” It’s a familiar question, and it gets to the heart of why compliance matters.
Security threats evolve constantly. Regulations grow more complex every year. And the cost of getting it wrong keeps climbing. GDPR fines can reach €20 million or 4% of global revenue. Non-compliance with HIPAA brings severe financial penalties. But the real damage often goes beyond fines—lost trust, operational disruption, and exposure of sensitive customer data can be devastating.
Here’s the sobering reality: 74% of all cyber breaches are caused by human factors. That means your biggest vulnerability isn’t necessarily your firewall or encryption—it’s your people. Without clear policies and consistent training, employees can’t make good security decisions. They share passwords for convenience. They click suspicious links. They install unapproved software. And each of these actions creates risk.
An effective information security policy changes that. It sets clear expectations. It guides the implementation of technical controls. It helps your organization meet regulatory requirements while improving efficiency. Most importantly, it creates a foundation for building a culture of protection across your entire team.
The good news? You don’t need to figure this out alone. With the right approach and local expertise, achieving compliance becomes manageable—even for organizations without dedicated security teams.
I’m Jay Baruffa, and over 20 years of working with complex networks, cybersecurity, and compliance requirements, I’ve helped businesses across Northeast Ohio build practical security programs. My focus has always been on reducing risk through clear IT security policy compliance strategies that actually work in the real world—not just on paper.
Understanding IT Security Policy Compliance and Its Importance
At its core, IT security policy compliance is about safeguarding your organization’s most valuable assets: its information and the systems that process it. We often talk about the “CIA triad” of information security: Confidentiality, Integrity, and Availability.
- Confidentiality: Ensuring that sensitive information is accessed only by authorized individuals—protecting customer data, financial records, and proprietary business plans.
- Integrity: Maintaining the accuracy and completeness of data, ensuring it hasn’t been tampered with or corrupted.
- Availability: Ensuring that authorized users can access information and systems when needed. Downtime from a cyberattack or system failure can bring a business to its knees.
Why is this so crucial for organizations in Painesville, Mentor, Cleveland, and across Northeast Ohio? Because the digital landscape is fraught with risks. A staggering 74% of all cyber breaches are caused by human factors. This statistic from Mimecast underscores a critical truth: human risk is the biggest security gap. People, not just technology, are often the weakest link.
Without a robust IT security policy compliance framework, employees might inadvertently open the door to threats—falling for phishing scams, using weak passwords, or mishandling sensitive data. The consequences range from data breaches and ransomware attacks to significant financial penalties and reputational damage.
Ensuring IT security policy compliance isn’t just about avoiding fines; it’s about building resilience, protecting customers, and maintaining trust. If you’re looking to strengthen your defenses, exploring our cybersecurity solutions is a great first step.
Building a Culture of IT Security Policy Compliance
Given that human factors are behind most breaches, fostering a strong culture of security awareness is paramount. A truly secure organization isn’t one with just the best technology, but one where every employee understands their role in protecting information.
This involves:
- Security Awareness Training: Regular, engaging training sessions educating employees about common threats like phishing, malware, and social engineering.
- Employee Training: Beyond general awareness, specific training on company policies, data handling procedures, and incident reporting is essential. This is particularly important when bringing on new staff, new security risk are introduced, so onboarding must include comprehensive security education.
- Phishing Simulations: Periodically testing employees with simulated phishing attacks reveals vulnerabilities and provides teachable moments without real-world consequences.
- Accountability: Establishing clear expectations and consequences for policy violations ensures that security isn’t seen as optional.
A strong security culture transforms abstract rules into practical habits that protect our organization daily.
The Role of Senior Management
For any IT security policy compliance program to succeed, active involvement from senior management is non-negotiable. Their responsibilities include:
- Executive Buy-in: When leaders champion security, it sends a clear message that security is a priority, not just an IT concern.
- Resource Allocation: Implementing effective security policies requires time, budget, and personnel. Senior management must ensure adequate resources are allocated.
- Policy Enforcement: Leaders must approve policies and ensure they are enforced consistently, leading by example and addressing non-compliance.
- Strategic Alignment: Security policies should align with overall business objectives, supporting rather than hindering organizational goals.
- Governance Oversight: Senior management is responsible for regular reviews of security posture, risk management strategies, and compliance efforts.
Without this leadership, security initiatives can flounder, and the critical goal of IT security policy compliance becomes much harder to achieve.
Key Components of an Effective Policy
An effective information security policy isn’t just a single document; it’s a comprehensive framework outlining our organization’s approach to protecting information. It serves as a living guide, coordinating security programs and communicating our measures to employees, third parties, and auditors.
When we develop these policies, we ensure they are enforceable, practical, regularly updated, and focused on business goals. Key elements include:
- Purpose and Scope: Clearly defines the policy’s objectives and to whom it applies (all employees, contractors, systems, and data).
- Acceptable Use: Outlines proper use of company IT resources, including internet, email, software, and hardware.
- Access Control: Specifies who can access what information and under what conditions, including the principle of least privilege. A common issue we see is half staff have too much access to data, which this policy addresses.
- Encryption Standards: Defines when and how encryption should be used for data at rest and in transit.
- Data Backup and Recovery: Establishes procedures for regularly backing up critical data and restoring it in the event of a loss or disaster. For more on this, check out our backup & business continuity solutions.
- Incident Response: Details the steps to take when a security incident occurs, from detection and containment to recovery and post-incident analysis.
- Data Classification: Categorizes data based on sensitivity (e.g., public, internal, confidential, restricted) to apply appropriate security controls.
Resources like SANS Institute security policy templates provide excellent starting points, offering best practices from experienced subject matter experts.
Types of Security Policies: Program, Issue, and System-Specific
The National Institute of Standards and Technology (NIST) outlines three distinct types in Special Publication (SP) 800-12:
- Program Policies: The highest-level strategic blueprints communicating senior management’s intent regarding information security. Broad, technology-agnostic, and focused on “what” we want to achieve.
- Issue-Specific Policies: These address particular security concerns such as acceptable use of email, remote access, or social media, providing concrete guidance on specific topics.
- System-Specific Policies: The most detailed, focusing on individual systems with specific configurations, operational procedures, and security controls for assets like firewalls, web servers, or critical applications.
Understanding these types helps structure IT security policy compliance documentation effectively. If you need assistance, our IT consulting and advisory services can help.
Technical Controls and System Hardening
While policies define what we need to do, technical controls are the how. System hardening reduces the attack surface, making systems more resilient to threats.
Key technical controls include:
- CIS Benchmarks: We reference Center for Information Security (CIS) benchmarks for operating systems and cloud environments to ensure systems are hardened against known vulnerabilities.
- Password Complexity and Management: Strong password requirements enforced through system settings, often complemented by password managers.
- Multi-Factor Authentication (MFA): Requiring two or more verification factors significantly strengthens access control, especially for remote access and sensitive applications.
- Patch Management: Regularly updating software with the latest security patches closes known vulnerabilities. Our managed services include robust patch management for clients across Northeast Ohio.
- Network Segmentation: Dividing the network into isolated segments helps contain breaches and restrict lateral movement.
- Firewalls and IDS/IPS: These technologies monitor and control network traffic, blocking malicious activity and alerting us to suspicious patterns.
These technical controls are the practical application of our IT security policy compliance efforts against the changing threat landscape.
Navigating Regulatory Frameworks and Standards
For businesses in Northeast Ohio, navigating regulatory and security compliance frameworks is a necessity. These frameworks provide structured guidelines to protect sensitive data, manage risks, and meet legal obligations. Regulatory and security compliance frameworks ensure security is built into operational processes.
| Framework | Primary Focus | Applicability | Key Requirements |
|---|---|---|---|
| GDPR | EU data privacy law protecting personal data of EU citizens. | Applies if your Ohio business processes data of EU residents. | Strict security, consent, and data subject rights. Fines up to EUR 20 million or 4% of global revenue. |
| HIPAA | US law protecting patient health information (PHI). | Mandatory for healthcare providers, insurers, and business associates handling PHI. | Administrative, physical, and technical safeguards required. |
| PCI DSS | Global standard for securing credit card data. | Any business that processes, stores, or transmits credit card data. | 12 key requirements including encryption, access control, and vulnerability management. |
| ISO 27001 | International standard for Information Security Management Systems (ISMS). | Voluntary but widely recognized for demonstrating robust information security. | Risk-based approach across confidentiality, integrity, and availability. |
| NIST CSF | Voluntary framework to manage cybersecurity risks. | Recommended for organizations wanting a structured security program. | Five functions: Identify, Protect, Detect, Respond, Recover. |
| SOC 2 | Assurance framework for service organizations handling customer data. | Relevant for technology-enabled service providers. | Based on Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, Privacy. |
| Ohio HB 96 | Ohio state law providing an affirmative defense for businesses adopting a recognized cybersecurity framework. | Relevant for Ohio organizations seeking legal protection. | Demonstrate adherence to a recognized framework such as NIST CSF or ISO 27001. Learn more: Ohio HB 96: A Practical Path to Compliance. |
Meeting Global and Industry-Specific Requirements
Even businesses solely operating in Northeast Ohio might be subject to global regulations. The GDPR is a European Union data privacy law that applies to organizations handling EU citizen data regardless of location. If you have customers in the EU, even from Cleveland or Akron, you must comply. Failure can lead to fines up to EUR 20 million or 4% of global revenue.
For healthcare organizations throughout Ohio, The HIPAA Security Rule mandates strict data protection measures for Protected Health Information (PHI), including administrative, physical, and technical safeguards.
Any business in Lake County or Summit County that processes credit card data must adhere to The PCI DSS, which outlines 12 key security requirements designed to protect cardholder data.
Frameworks like FedRAMP (for cloud providers working with federal agencies) or The CMMC framework (for DoD contractors) are relevant for Ohio businesses in the federal or defense supply chain.
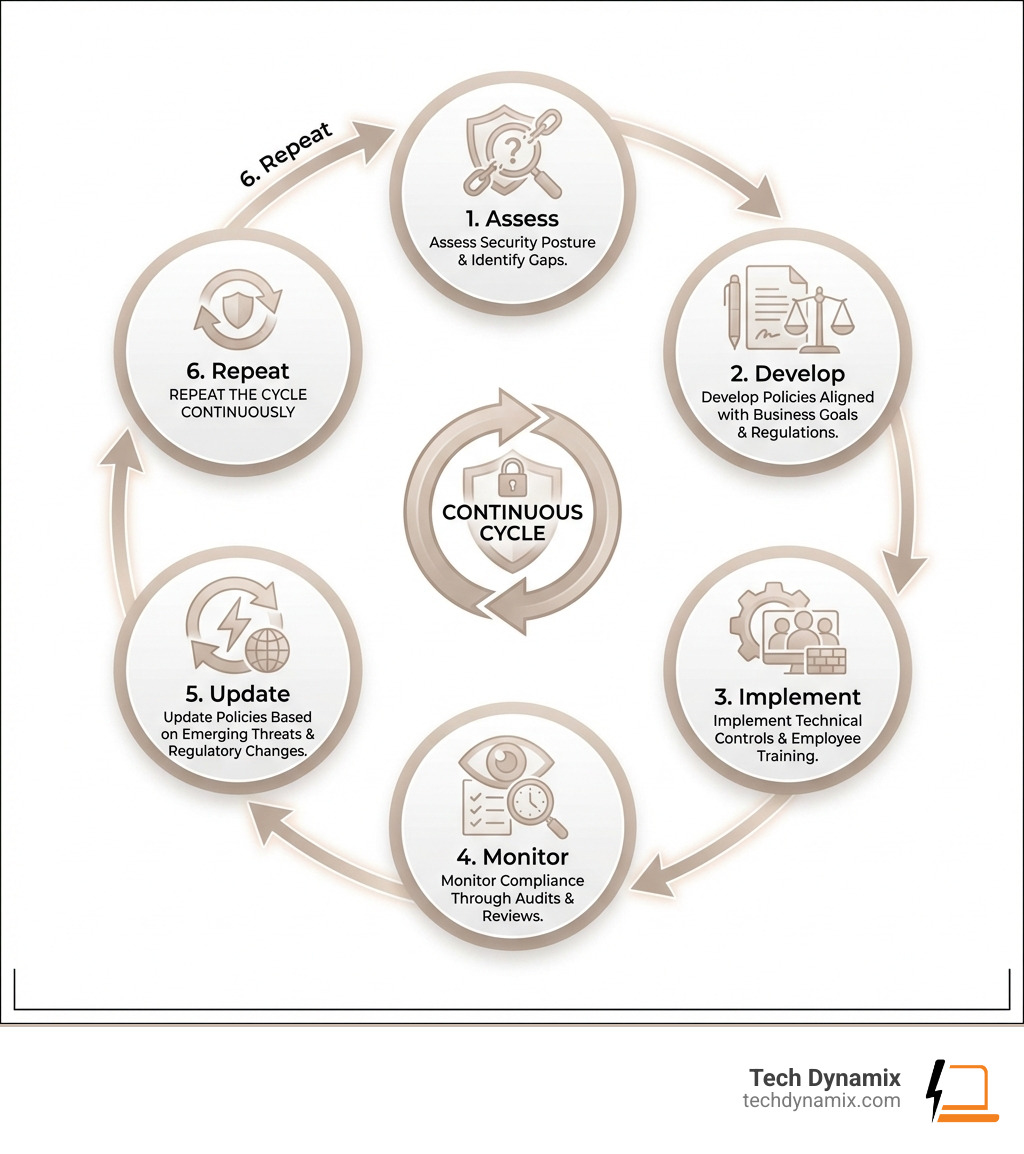
Leveraging Frameworks for Continuous Improvement
Adopting a compliance framework isn’t just about checking boxes; it’s about embedding continuous improvement into security operations. These frameworks provide a roadmap for:
- Gap analysis: Assess your current security posture against best practices and identify improvements.
- Risk assessment: Frameworks like The NIST Cybersecurity Framework (CSF) help identify, assess, and prioritize cybersecurity risks.
- Operational resilience: Build processes that help you withstand and recover from incidents with less downtime.
- Audit readiness: Align documentation and controls with auditor expectations to streamline compliance reviews.
These frameworks keep your approach to IT security policy compliance systematic, comprehensive, and adaptable.
Best Practices for Maintaining Compliance
Achieving IT security policy compliance is a journey, not a destination. The digital world is dynamic, with new threats and regulations emerging constantly. Therefore, maintaining compliance requires ongoing vigilance and a commitment to best practices.
- Regular Audits: We conduct regular internal and external audits to verify that our security controls are functioning as intended and that our policies are being followed. This helps us catch deviations before they become major issues.
- Policy Reviews: Our policies aren’t static documents. We review and update them annually, or whenever there’s a significant change in our business operations, technology, or the regulatory landscape. This ensures they remain relevant and effective.
- Vulnerability Management: This involves continuously identifying, assessing, and remediating vulnerabilities in our systems and applications. Regular vulnerability scans and penetration testing are crucial components of this practice.
The cost of non-compliance can be far-reaching. As failure to comply with security regulations can lead to severe financial penalties, reputational damage, and increased exposure to cyber threats. It’s not just about the fines; it’s about the erosion of trust and the potential loss of customers and business opportunities.
Assessing Your Current Security Posture
Before we can effectively maintain compliance, we first need to understand where we stand. Assessing our current security posture is a critical step in identifying weaknesses and prioritizing our efforts.
- Internal Audits: Our teams regularly conduct internal audits to evaluate the effectiveness of our security controls and adherence to our policies. This self-assessment helps us proactively identify issues.
- Third-Party Assessments: For an unbiased and comprehensive review, we often recommend compliance & security audits performed by independent third parties. These assessments can provide valuable insights and validate our internal efforts.
- Identifying Gaps: The primary goal of any assessment is to identify gaps between our current state and the desired state of compliance, whether that’s against a specific regulation (like HIPAA for healthcare in Hudson, Ohio) or a framework (like NIST CSF).
- Remediation Planning: Once gaps are identified, we develop a clear remediation plan outlining the steps needed to address them, assigning responsibilities, and setting realistic timelines.
This systematic approach ensures that our IT security policy compliance efforts are always informed and targeted.
Managing Third-Party and Supply Chain Risk
In today’s interconnected business world, our security is often only as strong as our weakest link, and that link can often be found in our supply chain. Many organizations in the Greater Cleveland Area rely on third-party vendors for everything from cloud services to specialized software. Each of these relationships introduces potential risks that must be managed as part of our IT security policy compliance.
- Vendor Assessments: Before engaging with a new vendor, we conduct thorough security assessments to evaluate their compliance posture and security practices. This includes reviewing their own policies, certifications, and incident response capabilities.
- Service Level Agreements (SLAs): Our contracts with third-party vendors clearly define their security responsibilities, data protection measures, incident notification requirements, and our rights to audit their security practices.
- NIST Secure Software Development Framework (SSDF): If we’re working with vendors who develop software, we encourage them to align with frameworks like The NIST Secure Software Development Framework (SSDF). This framework emphasizes secure design, coding, testing, and maintenance to reduce vulnerabilities throughout the software lifecycle.
- Data Processing Agreements: For vendors who handle sensitive data on our behalf, we establish formal data processing agreements that clearly outline how they will protect our data and comply with relevant regulations.
By proactively managing third-party and supply chain risks, we extend our IT security policy compliance efforts beyond our organizational boundaries, creating a more secure ecosystem for our business and our clients.
Frequently Asked Questions about IT Security Policy Compliance
Here are some of the most common questions we encounter from businesses in Northeast Ohio:
What is the main purpose of an IT security policy?
The main purpose is to communicate senior management’s intent regarding information security. It sets high-level principles, goals, and objectives that guide overall security strategy—defining “what” we need to protect and “why.” It provides a baseline to establish procedures, reduce risks, and ensure everyone understands their role in safeguarding assets. It also serves as a communication tool for third parties and auditors.
How often should security policies be reviewed and updated?
We recommend reviewing and updating security policies at least annually. However, they should also be updated whenever there are significant changes to business operations, technology infrastructure, or the regulatory landscape. Emerging threats, new deployments, staffing changes, or regulatory updates (like Ohio HB 96) all warrant re-evaluation. Continuous monitoring ensures policies remain relevant and effective.
What are the most common consequences of non-compliance?
The consequences can be severe and multifaceted:
- Financial Penalties: Regulatory bodies like those enforcing GDPR, HIPAA, and PCI DSS can levy hefty fines that far outweigh the cost of implementing proper cybersecurity measures.
- Legal Litigation: Non-compliance can lead to lawsuits from customers, partners, or employees whose data was compromised.
- Loss of Trust: A breach due to non-compliance can severely damage reputation, leading to lost customers and business opportunities.
- Operational Disruption: Security incidents often cause downtime, impacting productivity and revenue. Ransomware attacks can completely halt operations.
- Increased Vulnerability: A lack of compliance means security gaps, leaving organizations more susceptible to future attacks.
The cost of non-compliance isn’t just monetary; it impacts your ability to operate and your long-term viability.
Conclusion
Navigating the complexities of IT security policy compliance is a critical undertaking for any business today, especially for those of us operating in the dynamic environment of Northeast Ohio. From understanding the foundational elements of an effective policy to adhering to the major regulatory frameworks, a proactive and practical approach is essential.
We’ve explored why clear policies matter, how they drive technical controls, and the role senior management and employee awareness play in building a culture of security. We’ve also highlighted the consequences of non-compliance: fines, downtime, legal exposure, and loss of trust.
At Tech Dynamix, we understand these challenges. For over 20 years, we’ve provided high-quality IT consulting and managed IT services to small and mid-size businesses across Northeast Ohio. Our local expertise spans proactive IT support, robust cybersecurity solutions, cloud management, backup and disaster recovery, and ongoing helpdesk services. We’re here to be your dependable all-in-one technology partner, so your organization can meet its IT security policy compliance obligations and reduce risk.
Don’t leave your organization vulnerable to evolving threats and regulatory penalties. Let us help you assess your current posture, strengthen your policies, and implement the right controls.
Schedule a Compliance & Security Audit with Tech Dynamix today and take a significant step toward a more secure and compliant future.



