What Comprehensive IT Services Actually Include (And Why It Matters)
Comprehensive IT services are all-in-one technology management solutions where a single provider handles your entire IT environment — from cybersecurity and cloud to help desk support and compliance.
Here’s a quick breakdown of what’s typically included:
| Service Area | What It Covers |
|---|---|
| 24/7 Monitoring & Help Desk | Continuous system oversight and live user support |
| Cybersecurity | Threat detection, ransomware protection, endpoint security |
| Cloud & Microsoft 365 | Migration, management, and ongoing optimization |
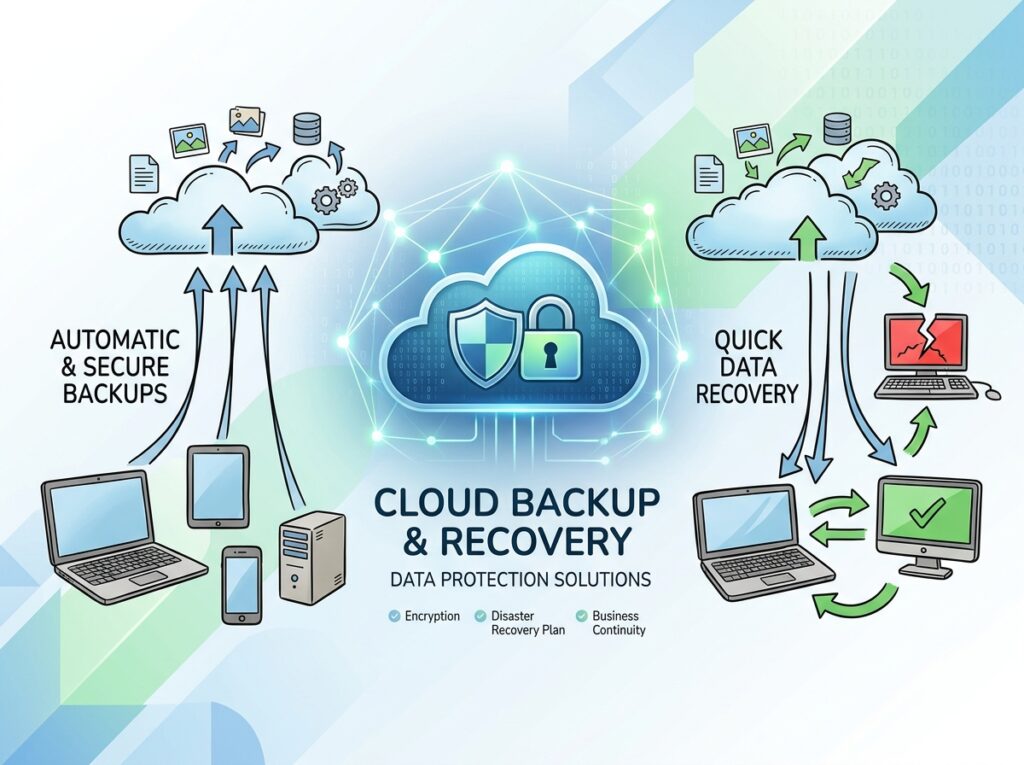
| Backup & Disaster Recovery | Automated backups, fast restoration, business continuity |
| Network Management | Firewall, infrastructure, VoIP, and connectivity |
| Compliance & Audits | HIPAA, regulatory requirements, security audits |
| IT Strategy & Consulting | Roadmaps, assessments, and technology planning |
The core idea: instead of patching together multiple vendors or reacting to problems after they happen, you get one proactive partner managing everything.
This matters more than ever. Consider that 61% of small and mid-sized businesses are hit by a cyberattack every year, and a new attack occurs every 11 seconds. Yet most SMBs still run their IT reactively — fixing things only after they break. Following established frameworks like the NIST Cybersecurity Framework is essential, but many small businesses lack the resources to implement them on their own.
That approach is expensive. It’s also risky.
I’m Jay Baruffa, founder of Tech Dynamix, and with over 20 years of hands-on experience in IT infrastructure, cybersecurity, and comprehensive IT services across Northeast Ohio, I’ve seen how the right managed IT strategy transforms businesses from reactive to resilient. In this guide, I’ll walk you through everything included in a truly all-in-one IT package — so you know exactly what to expect and what to look for.

Basic comprehensive IT services vocab:
What Defines Comprehensive IT Services?

To understand comprehensive IT services, we first have to look at what they aren’t. For decades, the standard model was “Break/Fix.” Your computer stops working, you call a guy, he comes out, fixes it, and sends you a bill. This creates a fundamental conflict: your IT provider only makes money when your business is suffering from downtime.
Managed services flip that script. With a comprehensive approach, we focus on proactive maintenance. We are incentivized to keep your systems running perfectly because we charge a flat monthly fee. If your systems stay up, we both win.
In our Managed IT Services Complete Guide, we emphasize that this model is about total infrastructure management. It includes 24/7 monitoring, where software “agents” watch your servers and workstations for signs of failure before they actually crash. If a hard drive starts showing errors at 2:00 AM in Willoughby, we know about it before your employees even sit down with their morning coffee.
| Feature | Traditional Break/Fix | Comprehensive Managed IT |
|---|---|---|
| Approach | Reactive (Wait for trouble) | Proactive (Prevent trouble) |
| Costs | Unpredictable spikes | Fixed monthly investment |
| Downtime | High (Waiting for repair) | Minimal (Issues solved early) |
| Security | Basic/Manual updates | Continuous 24/7 monitoring |
| Strategy | None | Long-term technology roadmap |
Whether it is remote support for a quick software glitch or onsite hardware repairs, the goal is a seamless environment where technology “just works.”
Core Components of an All-in-One IT Package
When you sign up for comprehensive IT services, you aren’t just getting a help desk phone number. You are gaining a full-scale IT department. At Tech Dynamix, we bundle the most critical tech needs into a single, cohesive strategy.
Proactive Cybersecurity and Compliance
In today’s world, security isn’t an “add-on”-it’s the foundation. With a cyberattack occurring every 11 seconds, we implement multi-layered cybersecurity solutions that go far beyond basic antivirus.
This includes:
- Threat Detection: Real-time monitoring of network traffic to spot anomalies.
- Ransomware Protection: Specialized tools to block encryption attempts and isolate infected devices.
- Compliance & Security Audits: For our clients in healthcare (HIPAA) or financial services, we perform regular compliance and security audits to ensure you meet strict regulatory standards.
- Endpoint Protection: Securing every laptop, desktop, and mobile device that connects to your network.
- Identity Management: Managing user permissions and enforcing Multi-Factor Authentication (MFA) across your environment.
Cloud Integration and Business Continuity
The modern office isn’t just a physical room in Mentor or Painesville; it’s in the cloud. We provide expert Microsoft 365 cloud support to help your team collaborate from anywhere. But moving to the cloud is only half the battle; you also need to ensure that data is safe.
Our backup and business continuity services ensure that if a server fails or a natural disaster hits Northeast Ohio, your data is redundant and recoverable. We don’t just “back up” files; we create a disaster recovery plan that allows you to boot up virtual versions of your servers in minutes, not days. This is a key part of any digital transformation strategy-ensuring that as you grow, your data remains accessible and resilient.
Communication and Mobility
A truly all-in-one package also handles how you talk to your customers. We offer VOIP systems and ISP brokerage to replace aging phone lines with modern, feature-rich internet-based phones. Additionally, with more employees working on the move, our MDM and mobile fleet repairs allow us to secure and manage the smartphones and tablets your team uses every day.
Why Businesses Choose Comprehensive IT Services
The shift toward outsourcing isn’t just about tech—it’s about the bottom line. Research shows that 60% of companies that suffer a major cyberattack go out of business within six months. For a small business in Lake County, that is a terrifying reality.
Comprehensive IT services provide a safety net. By investing in IT support that saves you money, you trade high-cost emergency repairs for a predictable monthly budget.
Other key drivers include:
- Cost Efficiency: You get access to a team of experts for less than the cost of one full-time in-house IT manager.
- Downtime Reduction: Proactive patching and 24/7 monitoring stop “tech fires” before they start.
- Strategy & Modernization: We don’t just fix what’s broken; we help you plan for the future. This includes managed IT insights that help you understand where your tech spend is going and how it can be optimized.
Strategic Growth with Comprehensive IT Services
We believe IT should be a growth engine, not a line-item expense. Through IT consulting and advisory services, we act as your “Virtual CIO” (vCISO). We help you implement automation services to handle repetitive tasks, gaining efficiency across your entire workforce.
Whether you need to implement ERP solutions to manage your manufacturing floor in Eastlake or need a 3-year technology roadmap to scale your healthcare practice, we ensure your tech stack is ready for the journey.
Selecting the Right Provider for Your Organization
Not all providers are created equal. When searching for comprehensive IT services, you need to look past the sales pitch. Start with Business IT Solutions 101: look for a provider that understands your specific industry’s pain points.
Key considerations should include:
- Service Level Agreements (SLAs): How fast do they promise to respond when things go wrong?
- Vendor Management: Will they talk to your internet provider or software vendors for you, or do they make you do the legwork?
- Scalability: Can they support you when you grow from 10 employees to 50?
- Security-First Mindset: Do they include advanced security, or is it an extra fee?
Check out our Why Us page to see how we differentiate ourselves through local expertise and a “human-first” approach to tech support.
Regional vs. National Comprehensive IT Services
You’ll find many national “mega-providers” out there, but for businesses in Northeast Ohio, there is a distinct advantage to staying local. A national provider might have a call center in another time zone, but they can’t send a technician to your office in Chardon or Mentor if your switch dies.
At Tech Dynamix, we provide:
- Onsite Support: We are right here in the Greater Cleveland Area. If a problem can’t be fixed remotely, we’re in our trucks and on the way.
- Personalized Service: You aren’t just a ticket number. We know your team, your office layout, and your business goals.
- Local Network Connectivity: We understand the local ISP landscape in Lake and Geauga Counties, helping you get the best network connectivity for your location.
- Staff Augmentation: If you already have a small IT team, we can provide staff augmentation to help with big projects or provide specialized security expertise.
Frequently Asked Questions about Managed IT
What is the difference between fully managed and co-managed IT?
Fully managed IT means we are your entire IT department. We handle everything from the “on” button to the cloud. Co-managed IT is a hybrid model where we partner with your existing internal IT person. We might handle the 24/7 monitoring and security (the “boring” stuff), while they focus on high-level business software and internal projects. This is a great way to add scalability to a lean team.
How much do comprehensive IT services cost?
Pricing typically follows a per-user or per-device model. This makes costs predictable. Instead of a $5,000 bill because a server died, you pay a consistent monthly fee that covers the maintenance to prevent that failure in the first place. When you factor in the ROI of reduced downtime and the prevention of cyberattacks, the services often pay for themselves.
How does IT management support remote workforces?
We make remote work secure and simple. This involves setting up secure VPNs, managing Microsoft 365 cloud support for file sharing, and using MDM & mobile fleet repairs to ensure that a laptop used in a home office in Mayfield Heights is just as secure as one in the main office.
Conclusion
Technology shouldn’t be a headache—it should be a competitive advantage. By choosing comprehensive IT services, you’re not just buying tech support; you’re buying peace of mind. You’re ensuring that your business in Northeast Ohio is protected against modern threats, optimized for the cloud, and supported by a team that cares about your growth.
Ready to stop worrying about your tech and start focusing on your business? Explore our Comprehensive IT Services and let’s build a technology roadmap that works for you.