Why AI Security Companies Are Essential for Modern Business Protection
An ai security company specializes in protecting AI systems from emerging threats while using AI to defend against increasingly sophisticated cyberattacks. Here’s what sets them apart:
Key Capabilities of AI Security Companies:
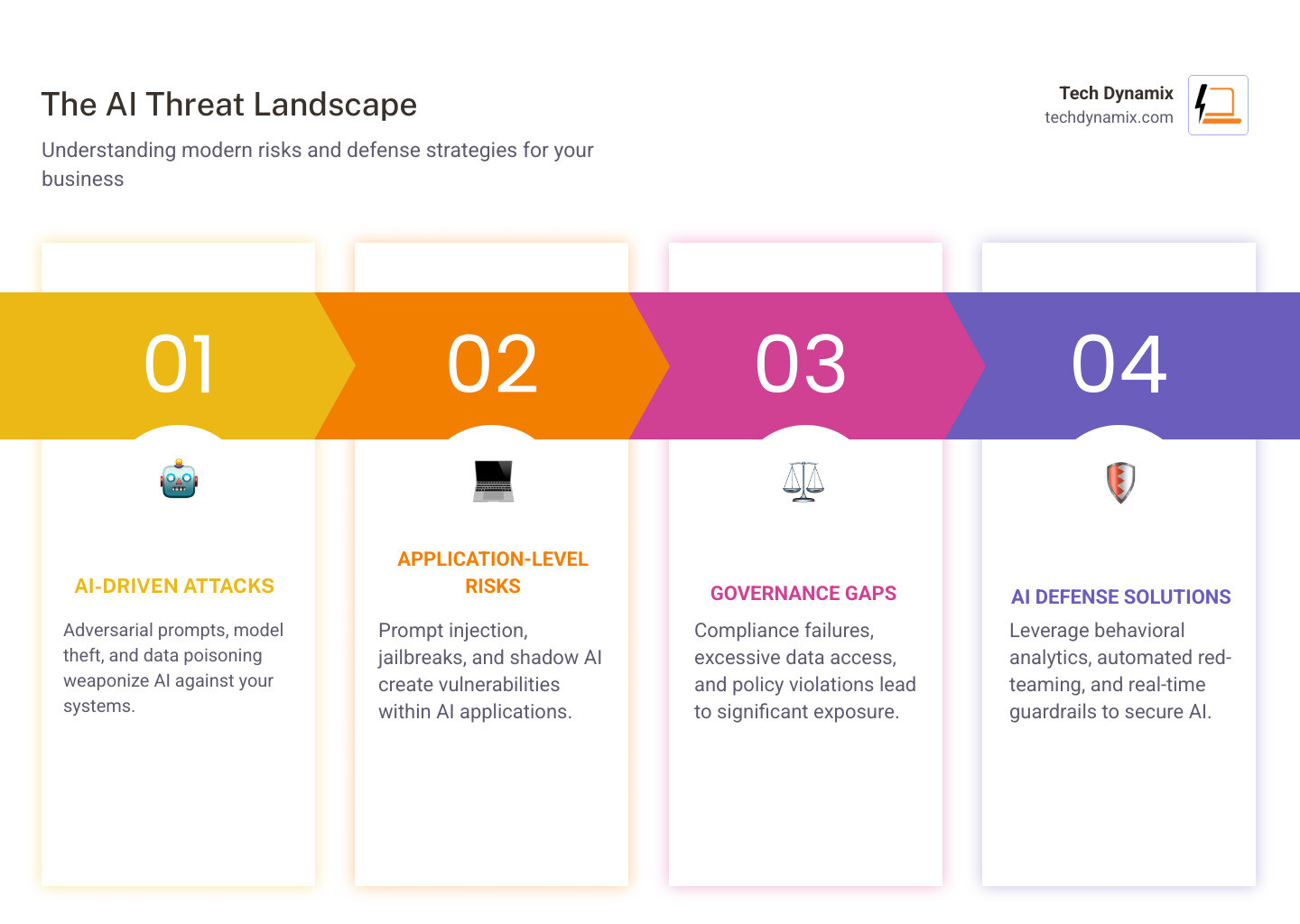
- AI Model Protection – Defend against adversarial prompts, model theft, and data poisoning.
- Proactive Threat Detection – Use behavioral analytics to identify risks before they escalate.
- Automated Response – Implement remediation and endpoint isolation at machine speed.
- Comprehensive Coverage – Secure endpoints, networks, and cloud environments across the tech stack.
- Continuous Testing – Conduct automated red-teaming and compliance monitoring.
The rise of AI has created a unique challenge. Cybercriminals are weaponizing AI to launch sophisticated attacks—74% of IT security professionals have already seen critical impacts from AI-fueled cyberattacks. Conversely, AI-powered defense systems can detect threats and analyze behavior anomalies at a scale impossible for human teams alone.
Traditional security tools rely on signature-based detection and static rules that can’t keep up with threats like prompt injection or AI agents probing vulnerabilities. Modern threats demand defenses that understand context, learn from patterns, and adapt without constant manual intervention.
For mid-size businesses handling sensitive data, the stakes are high. A single AI failure can trigger legal liability and damage brand trust. Many organizations feel they must choose between innovating with AI or slowing down for security. The right ai security company eliminates this tradeoff by building protection directly into your AI strategy.
I’m Jay Baruffa, and over the past 20 years, I’ve helped Northeast Ohio businesses steer complex IT challenges, including the emerging risks posed by AI. Selecting the right partner means understanding how different solutions address threats across your entire technology environment.
Primary Risks and the Dual Role of AI in 2026
As we look towards 2026, the landscape of AI security risks is evolving rapidly. AI is a double-edged sword, creating new vulnerabilities while offering powerful tools for defense. For businesses in Northeast Ohio, understanding these risks is the first step towards protection.
AI as a Source of Vulnerabilities: Offensive AI
Threat actors are increasingly leveraging “offensive AI” to improve their attacks. Primary risks include:
- Adversarial Prompts and Prompt Injection: Manipulating input to an AI model to extract sensitive data or bypass safety filters.
- Model Theft and Data Poisoning: Attempting to steal proprietary models or injecting malicious data into training sets to cause flawed behaviors.
- LLM Vulnerabilities: Susceptibility to jailbreaking, data leaks, and the generation of harmful content, as highlighted in the OWASP Top 10 for LLMs.
- Shadow AI: The uncontrolled use of AI tools by employees. Research shows 52% of U.S. Employees Are Willing to Break Policy to Use AI, leading to data privacy breaches.
- Agentic AI Risks: Autonomous AI systems that can execute tasks and interact with other systems, potentially exploiting vulnerabilities at machine speed.
- AI-Powered Malware: Approximately 80% of Malware is Powered by AI, making it more adaptive and capable of evading traditional detection.
These tactics highlight a critical need for businesses in Cleveland and Akron to rethink their cybersecurity strategies. Explore our cybersecurity solutions for more information.
AI as a Shield: Defensive AI
“Defensive AI” leverages machine learning to protect systems and automate responses at scale.
- Real-time Anomaly Detection: AI analyzes network traffic and user behavior to establish baselines. Any deviation is flagged as a potential threat.
- Behavioral Analytics: Identifying suspicious patterns indicative of insider threats. This is vital since Half Staff Have Too Much Access to Data.
- Automated Incident Response: AI can trigger immediate responses, such as isolating endpoints or disabling accounts, which is crucial for mitigating fast-moving attacks.
- Threat Intelligence: Processing global feeds to identify emerging attack vectors and proactively strengthen defenses.
Specialized Approaches in the AI Security Market
The market for AI security is expanding, with innovative platforms designed for the complexities of modern threats. These solutions are building AI-native architectures rather than just adding features to legacy tools.

Key Specialized Approaches:
- AI-Native Enterprise Protection: Applying self-learning AI to detect novel threats across networks, email, and cloud. These platforms learn an organization’s specific data to identify subtle deviations signaling emerging threats.
- Security for AI Apps and Agents: Focusing on the entire AI lifecycle through proactive red-teaming and real-time defense. These solutions address the OWASP Top 10 for LLMs and secure employee AI usage.
- LLM-Agnostic Security Platforms: Defending against risks like prompt injection and data leaks across various Large Language Models. These platforms integrate seamlessly with existing tech stacks to secure homegrown AI apps and code assistants.
- Model-Level Vulnerability Mitigation: Focusing on vulnerabilities inherent in AI models. These solutions use automated red teaming to identify risks like model inversion and data poisoning, often aligning with frameworks like MITRE ATLAS™.
- Attack Surface Visibility: Using AI to provide visibility into attacker movements across hybrid environments, including identity and SaaS, to detect stealthy lateral movements.
- Automated Machine Learning Security: Integrating directly into ML workflows to scan models from training to deployment. For example, integration with platforms like Databricks Unity Catalog provides continuous protection without disrupting development speed.
- Research-Driven Adaptive Defense: Combining input/output filtering with continuous agentic monitoring. These systems are custom to specific AI tools and workflows. For those interested in collaboration, consider joining an AI security community to stay updated on emerging vulnerabilities.
- Semantic Intelligence for Data Protection: Leveraging behavioral analysis to protect sensitive data across cloud and endpoints. These tools track data lineage and user interactions to identify risky patterns beyond simple keywords.
- Safety and Trust for Generative AI: Ensuring the security of communicative technology through stress-testing and dynamic runtime guardrails, utilizing large adversarial intelligence datasets to adapt to threats in real-time.
Core Security Features Across Platforms:
- AI Model Hardening: Protecting models from adversarial attacks and theft.
- Input/Output Filtering: Preventing malicious input and blocking sensitive output.
- Real-time Guardrails: Enforcing safety and compliance during AI runtime.
- Data Security Posture Management (DSPM): Classifying and protecting sensitive data.
- Automated Red Teaming: Continuously testing systems using adversarial techniques.
- Agentic AI Security: Specialized protection for autonomous AI agents.
Key Features of a Leading AI Security Company
When evaluating an ai security company, we look for features that provide robust, adaptive protection against modern AI-powered threats.
1. Real-time Anomaly Detection and Behavioral Analytics
Effective AI security detects deviations from normal behavior. Traditional security relies on static rules, which are easily outmaneuvered. A leading provider uses:
- Real-time Anomaly Detection: Continuous monitoring of network traffic and system logs to identify unusual patterns instantly.
- Behavioral Analytics: Learning the “normal” behavior of users and AI models. Any departure triggers an alert, which is crucial for detecting zero-day exploits and insider threats.
2. Automated Remediation and Response
Speed is paramount when facing machine-speed adversaries. A top-tier ai security company acts immediately:
- Automated Remediation: Threats are automatically contained by isolating endpoints or disabling accounts based on AI-driven conclusions.
- Human-in-the-Loop: For sensitive actions, security teams can approve AI-recommended responses with a single click, balancing automation with oversight.
3. LLM-Agnostic and Flexible Deployment
The AI landscape is diverse. A flexible provider understands that organizations use different models and strategies:
- LLM-Agnostic: Compatibility with a wide range of models ensures future-proofing.
- Flexible Deployment: Support for cloud-native, on-premises, or hybrid environments allows seamless integration into existing infrastructure.
4. Scalability and Comprehensive Coverage
As your AI footprint expands, the security solution must scale effortlessly, providing coverage across the entire AI lifecycle—from data ingestion and training to deployment and inference.
5. Advanced Vulnerability Testing and Forensics
Proactive testing is critical for continuous improvement:
- Automated Red Teaming: Continuously challenging systems with adversarial attacks. We monitor scientific research on LLM jailbreaking to inform these methodologies.
- Forensic Investigation: Providing detailed logs and root cause analysis to aid in rapid recovery and prevent future incidents.
These features empower businesses to accept AI confidently. We also believe in how to help people be AI confident through education and secure tools.
Integration, Compliance, and Choosing a Partner
Navigating AI security requires strategic planning to ensure technology fits your ecosystem and adheres to regulations.
Integrating AI Security with Existing Workflows
An effective ai security company ensures seamless integration with your current stack:
- SIEM/SOAR Integration: Platforms should feed threat intelligence into your existing management systems for a unified view.
- CI/CD Pipeline Integration: Security must be embedded into development workflows, performing automated scanning at every stage.
- AI-BOM (Bill of Materials): Maintaining an inventory of all AI assets is crucial for oversight and compliance.
AI-Native vs. AI-Bolted Solutions
| Feature | AI-Native Solutions | AI-Bolted Solutions |
|---|---|---|
| Foundation | Built for AI from the ground up | Traditional tools with added ML |
| Threat Coverage | Specialized in AI-specific threats | Focuses on traditional risks |
| Detection | Real-time behavioral analytics | Often signature-based |
| Adaptability | Continuously learns and adapts | Requires manual updates |
We recommend prioritizing AI-native solutions purpose-built for the unique challenges of the AI era.
AI Security Certifications and Compliance
For regulated industries, compliance is critical:
- Regulatory Mapping: Platforms should map AI systems to frameworks like HIPAA, NIST, or GDPR.
- OWASP Top 10 for LLMs: Adherence to these benchmarks indicates a commitment to addressing critical vulnerabilities.
- Certifications: Look for vendors with SOC 2 or ISO 27001. Our CyberCert SMB1001 Bronze Certification shows our dedication to robust security practices.
- Data Lineage: Understanding data origin and usage throughout the AI lifecycle is vital for auditing.
Our expertise in compliance & security audits helps businesses steer these requirements effectively.
Choosing the Right AI Security Partner
- Define Priorities: Identify your most critical AI assets and risks.
- Evaluate Depth: Ensure the solution offers true AI-native protection.
- Check Integration: Confirm it works with your SIEM/SOAR and CI/CD pipelines.
- Prioritize Results: Seek third-party validation and real-world case studies.
- Consider Expertise: Choose a partner with a proven track record in AI research.
Frequently Asked Questions
What is the difference between a traditional firm and an ai security company?
A traditional firm focuses on protecting IT infrastructure using established methods like firewalls and antivirus, which often rely on signature-based detection. While effective against known threats, they struggle with adaptive AI-driven attacks.
An ai security company specializes in protecting AI systems from specific threats like adversarial prompts and data poisoning. They employ real-time anomaly detection and behavioral AI to learn what “normal” looks like for your systems, allowing them to detect entirely new forms of attacks that traditional tools would miss.
Can an ai security company replace my existing IT team?
No, it augments and empowers them. AI security tools automate repetitive tasks like triaging alerts and analyzing vast datasets, freeing up human analysts for strategic issues and complex investigations. In an era of talent shortages, these solutions bridge the gap by increasing efficiency. Human oversight remains critical for ethical considerations and adapting strategies to unique business contexts. We focus on how to help people be AI confident to ensure your team remains productive and secure.
How does an ai security company protect against prompt injection?
They address this through a multi-layered approach:
- Input Filtering: Using NLP and machine learning to neutralize malicious prompts before they reach the model.
- Output Filtering: Preventing the model from generating unauthorized or harmful responses.
- Agentic Monitoring: Tracking AI behavior in real-time to flag actions outside defined parameters.
- Vulnerability Testing: Simulating attacks through automated red teaming to identify and fix weaknesses proactively. Our cybersecurity solutions include staying ahead of these evolving threats.
Conclusion
The evolution of AI presents both opportunities and security challenges. For businesses in Northeast Ohio, partnering with the right ai security company is a necessity for thriving in the digital era. From defending against AI-powered malware to securing applications from adversarial attacks, specialized protection is required.
At Tech Dynamix, we understand the needs of small and mid-size businesses. We help you steer the complexities of AI security, ensuring your ventures are protected by intelligent defenses. By integrating advanced insights with our local expertise, we provide cybersecurity solutions custom to your requirements, giving you the confidence to accept the power of AI.



