Why NIST Compliance Consulting Is Essential for Today’s Businesses
NIST compliance consulting helps organizations understand, implement, and maintain the cybersecurity standards set by the National Institute of Standards and Technology (NIST) — a non-regulatory agency of the U.S. Department of Commerce that develops the security frameworks most federal agencies and contractors are required to follow.
Here’s what you need to know at a glance:
| Question | Quick Answer |
|---|---|
| What is NIST? | A U.S. government agency that sets cybersecurity standards and frameworks |
| Who needs NIST compliance? | Federal agencies, government contractors, DoD suppliers, and organizations handling sensitive data |
| Key frameworks | NIST CSF 2.0, NIST SP 800-53, NIST SP 800-171 |
| Is it mandatory? | Required for federal contractors; strongly recommended for all others |
| Is it a one-time process? | No — it requires ongoing monitoring and periodic reassessments |
If you work with the U.S. government — or want to — NIST compliance isn’t optional. It’s the price of entry.
And even if you don’t have federal contracts, NIST frameworks are widely recognized as a gold standard for cybersecurity. Ignoring them means leaving your organization exposed to risks that are very real and growing every year.
But navigating these frameworks on your own? That’s where things get complicated fast. There are multiple overlapping standards, hundreds of security controls, and compliance requirements that shift as threats evolve. For most small and mid-sized businesses, it feels like a jungle.
I’m Jay Baruffa, founder of Tech Dynamix, and with over 20 years of hands-on experience in IT infrastructure, cybersecurity, and compliance, I’ve helped Northeast Ohio businesses cut through exactly this kind of complexity — including guiding organizations through NIST compliance consulting engagements that reduce risk without overwhelming their teams. This guide will walk you through everything you need to know, step by step.
Key NIST compliance consulting vocabulary:
- IT Security Policy Compliance
- Auditing IT Security Policy Compliance
- Automated IT Security Policy Compliance Systems
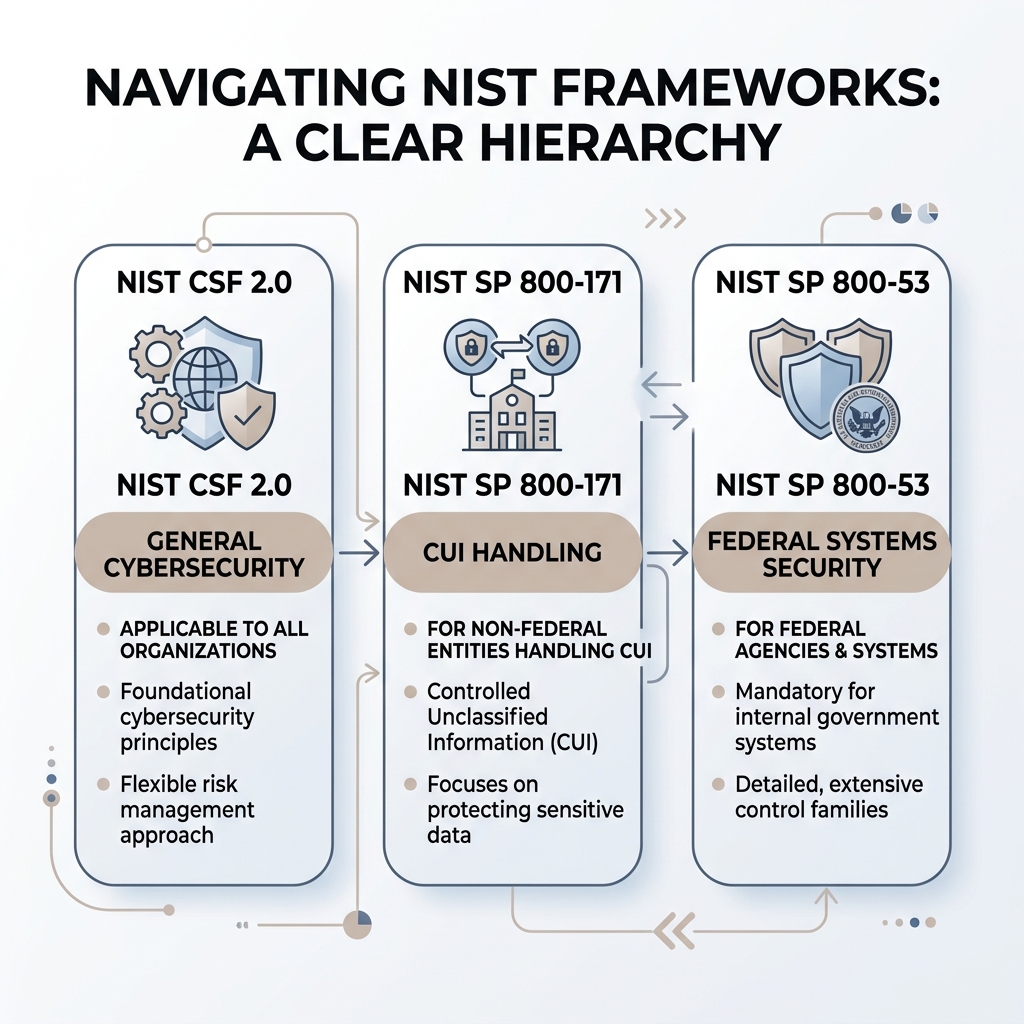
Understanding the NIST Frameworks: 800-53, 800-171, and CSF
In cybersecurity, NIST isn’t just one single checklist. It’s a library of different frameworks designed for different purposes. Depending on who your customers are and what kind of data you handle, you might need to align with one or more of these “Special Publications” (SP).
NIST 800-53: The Federal Gold Standard
This is the most comprehensive framework. NIST SP 800-53 provides a catalog of security and privacy controls for federal information systems. It contains nearly 1,200 controls in its latest revision (Rev. 5). While it was originally built for federal agencies, it’s often used by large organizations that want the highest level of assurance. Think of it as the “encyclopedia” of security controls.
NIST 800-171: Protecting CUI
If you are a non-federal organization—like a manufacturing firm in Mentor or a research lab in Cleveland—and you handle Controlled Unclassified Information (CUI) for the Department of Defense (DoD), GSA, or NASA, this is your primary framework. NIST SP 800-171 includes 110 security requirements broken across 14 control families. It is designed to be more flexible and less complex than 800-53, focusing specifically on how contractors protect government data on their own internal networks.
NIST CSF 2.0: The Flexible Foundation
The NIST Cybersecurity Framework (CSF) is the most “user-friendly” of the bunch. It was recently updated to version 2.0 and is now organized around six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. It’s industry-agnostic, meaning whether you’re a nonprofit in Chardon or a financial services firm in Mayfield Heights, you can use the CSF to build a resilient security posture from the ground up.
| Feature | NIST CSF 2.0 | NIST SP 800-171 | NIST SP 800-53 |
|---|---|---|---|
| Primary Audience | All organizations (voluntary) | Government contractors (CUI) | Federal agencies & high-security |
| Control Count | High-level outcomes | 110 Requirements | ~1,200 Controls |
| Focus | Risk management & maturity | Data protection (CUI) | Total system security/privacy |
| Best For | Building a security culture | Meeting DoD/DFARS contracts | Maximum compliance rigor |
Learn more about Tech Dynamix’s NIST Consulting Services
How NIST Relates to CMMC, ISO 27001, and SOC 2
One of the most common questions we get during NIST compliance consulting sessions is: “Wait, I also need CMMC or SOC 2—how do these fit together?”
The good news is that these standards aren’t mutually exclusive; they actually share a lot of DNA.
- CMMC (Cybersecurity Maturity Model Certification): For DoD contractors, CMMC Level 2 is essentially a mirror of NIST SP 800-171. If you satisfy the 110 practices of 800-171, you are well on your way to CMMC certification.
- DFARS (Defense Acquisition Federal Regulation Supplement): This is the legal clause in your contract that actually mandates NIST 800-171 compliance.
- ISO 27001 & SOC 2: While ISO 27001 is an international standard and SOC 2 is common for service providers, there is significant overlap. NIST alignment can often provide the technical evidence needed to “check the box” for these other audits, reducing duplicate work for your team.
- FISMA: This is the law that requires federal agencies to implement NIST 800-53.
More info about CMMC requirements
Why Your Business Needs NIST Compliance Consulting
Why bother with all this paperwork? Beyond the “because the government told me to” factor, there are tangible business benefits:
- Risk Reduction: NIST frameworks aren’t just red tape; they are proven strategies to prevent breaches. By following these guidelines, you’re addressing the most common ways hackers get in.
- Competitive Advantage: Being able to prove your security posture makes you a much more attractive partner to larger primes and government agencies.
- Legal Protection: In the event of an incident, being able to show that you followed a recognized federal standard can be a powerful defense against claims of negligence.
More info about cybersecurity solutions
The Strategic Path to NIST Compliance Consulting Success
Achieving compliance isn’t a sprint; it’s a structured journey. We’ve seen organizations try to DIY this process, only to get bogged down in the technical minutiae. A professional NIST compliance consulting approach breaks the “jungle” down into manageable trails.

Core Components of a NIST Compliance Program
To be “compliant,” you need more than just a antivirus software. You need a documented program. The core components usually include:
- Risk Assessments: A three-tiered review that looks at risks at the organizational level, the business process level, and the information system level.
- System Security Plan (SSP): This is the “Bible” of your security program. It documents exactly which controls you have in place, how they are implemented, and who is responsible for them.
- Security Controls: The actual technical and administrative safeguards (like multi-factor authentication or employee training).
- Plan of Action and Milestones (POAM): NIST knows you might not be perfect on day one. A POAM lists your gaps and sets a strict timeline for when you will fix them.
Conducting a NIST Gap Analysis
The first real step in any NIST compliance consulting engagement is the gap analysis. This is where we measure where you are versus where the framework says you need to be.
We start by defining the “boundary”—which parts of your network actually touch sensitive government data? Once we know the scope, we review your existing policies, interview your team, and perform technical scans. The result is a clear remediation strategy. Instead of guessing, you get a prioritized list of what to fix first based on risk and effort.
Explore Tech Dynamix’s NIST Advisory & Assessment Services
Timeline, Costs, and Overcoming Implementation Challenges
How long does this take, and what’s it going to cost? These are the big questions for any business owner in Lake County or the Greater Cleveland area.
The Timeline: From Chaos to Compliance
While every business is different, many organizations can reach a state of “readiness” in about three to six months.
- NIST CSF: Can often be assessed and aligned in as little as two weeks to a month.
- NIST 800-171: Typically takes 3-4 months to fully document and implement.
- NIST 800-53: Because of the sheer volume of controls, this can take 6 months to a year.
Factors affecting your timeline include the size of your organization, your current “technical debt” (how old your systems are), and how much time your staff can dedicate to the project.
Budgeting for Success
Budgeting for NIST isn’t just about the consulting fee. You need to consider:
- Remediation Costs: Do you need to upgrade servers or buy new encryption tools?
- Ongoing Monitoring: Compliance isn’t a “one and done” deal.
- Employee Training: Your team needs to understand the new rules.
Navigating IT security compliance
Benefits of Professional NIST Compliance Consulting
Why hire a consultant instead of just reading the PDF?
- Avoid Over-Scoping: One of the biggest mistakes businesses make is trying to secure everything to NIST standards. A consultant helps you narrow the scope to only what is required, saving you thousands in unnecessary hardware and labor.
- SPRS Scores: For DoD contractors, your NIST 800-171 score must be submitted to the Supplier Performance Risk System (SPRS). Scores range from a perfect +110 down to -203. We help you get that score as high as possible.
- Stakeholder Trust: When you can hand a potential client a professionally prepared SSP, it builds immediate confidence.
More info about IT consulting and advisory
Maintaining Continuous Compliance in a Shifting Threat Landscape
One of the most dangerous myths in IT is that compliance is a “certification” you get once and put on a shelf. In reality, NIST compliance is an ongoing process.
The Cycle of Continuous Monitoring
The threat landscape changes every day. A new vulnerability in Microsoft 365 or a new phishing tactic can render your previous controls obsolete. That’s why NIST emphasizes Continuous Monitoring.
This involves:
- Annual Reviews: Re-assessing your controls at least once a year.
- Incident Response Testing: Running “tabletop exercises” to make sure your team knows what to do if a breach happens.
- Automated Systems: Using tools that alert you the moment a security setting is changed or a policy is violated.
Streamlining IT security with automated systems
Qualifications to Look for in a NIST Consultant
If you’re looking for a partner in Northeast Ohio to help with your NIST compliance consulting, don’t just hire the cheapest IT shop. Look for credentials and experience that prove they understand the federal landscape:
- Certifications: Look for CISSP (Certified Information Systems Security Professional), CISA (Certified Information Systems Auditor), or CMMC-RP (Registered Practitioner).
- Experience: Have they actually written an SSP before? Do they understand the nuances of CUI?
- Local Presence: Having a partner in places like Willoughby or Highland Heights means they can be onsite for physical security audits and face-to-face strategy sessions.
More info about security services
Frequently Asked Questions about NIST Compliance
How long does it typically take to become NIST compliant?
For most SMBs in the Cleveland area, the journey takes 3 to 12 months. If you already have a mature IT setup, you might be ready in 90 days. If you’re starting from scratch with old hardware and no written policies, expect it to take closer to a year.
Is NIST compliance a one-time certification?
No. NIST itself does not issue “certifications.” You are either “compliant” (meeting the standards) or you aren’t. While programs like CMMC will eventually require a third-party audit every three years, the underlying NIST requirements require continuous monitoring and annual self-assessments to remain valid.
Who is required to comply with NIST 800-171?
Any non-federal organization that handles Controlled Unclassified Information (CUI). This includes:
- DoD contractors and subcontractors.
- GSA and NASA suppliers.
- Universities receiving federal research grants.
- State and local government agencies handling federal data.
Conclusion
Navigating the NIST jungle doesn’t have to be a solo expedition. Whether you are a manufacturer in Eastlake trying to protect your DoD contracts or a professional services firm in Mentor looking to level up your security, the frameworks provided by NIST offer a reliable map to safety.
At Tech Dynamix, we’ve spent over 20 years serving as a dependable technology partner for businesses across Northeast Ohio. We understand the local landscape—from the industrial corridors of Ashtabula to the tech hubs of Cuyahoga County. Our NIST compliance consulting services are designed to take the weight off your shoulders, allowing you to focus on growing your business while we handle the complexities of federal security standards.
Don’t wait for an audit or a breach to find out where your gaps are. Let’s work together to build a secure, compliant, and resilient future for your organization.



