Why IT Security Awareness Matters More Than Ever
IT security awareness is the knowledge and understanding employees need to protect their organization from cyber threats. Here’s what you need to know:
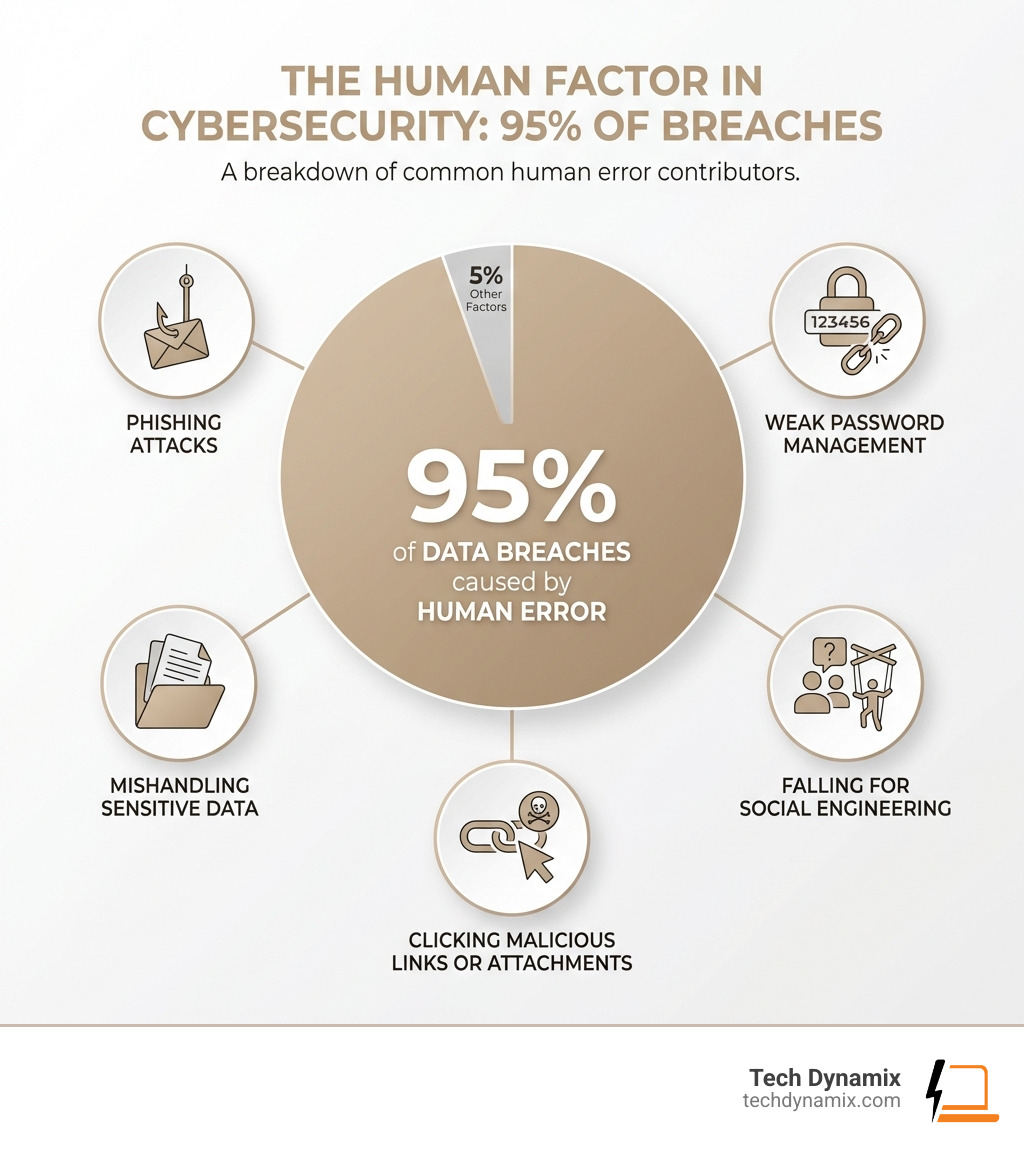
- Human error causes 95% of data breaches – including phishing, weak passwords, and mishandling sensitive data
- Key threats include phishing emails, malware, ransomware, social engineering, and insider threats
- Effective programs combine regular training, phishing simulations, clear policies, and leadership support
- Compliance frameworks like ISO 27001, NIS2, HIPAA, and GDPR mandate security awareness training
- Success metrics include phishing click rates, incident reporting frequency, and training completion rates
Your employees are your first line of defense against cyberattacks. But they’re also the most common entry point for threat actors. Over 3,700 phishing emails are reported every month at some organizations, yet simple awareness training has helped reduce compromised accounts by 96% and malware infections by 57% over three years.
The challenge is clear: technology alone can’t protect your business. Even the most sophisticated firewalls and antivirus software fail when an employee clicks a malicious link, uses a weak password, or falls for a social engineering scam. Building a security-aware culture transforms your team from potential vulnerabilities into active defenders of your organization’s data and reputation.
I’m Jay Baruffa, and over my 20+ years designing IT infrastructure and security solutions, I’ve seen how IT security awareness training can dramatically reduce risk and strengthen an organization’s cyber resilience. At Tech Dynamix, we help Northeast Ohio businesses build comprehensive security awareness programs that actually work.
The Foundation of IT Security Awareness
At its core, IT security awareness is about empowering every individual within an organization to become a proactive participant in its cybersecurity posture. It’s not merely about knowing what a threat is, but understanding the personal and organizational impact of that threat and knowing how to act responsibly. This collective understanding and responsible behavior form the bedrock of a strong defense against changing cyber threats.
Why is this so crucial for organizations, especially here in Northeast Ohio? Because, as the statistics starkly show, human error is the leading cause of data breaches. A 2023 IBM Security report found that an astonishing 95% of breaches are due to human mistakes. This isn’t about blaming employees; it’s about recognizing that the human element is often the easiest target for cybercriminals. Whether it’s falling for a convincing phishing email, using weak or reused passwords, or inadvertently mishandling sensitive data, these actions can open the door to devastating cyberattacks.
Effective IT security awareness programs aim to mitigate this risk by addressing the “human factors” that cybercriminals exploit. This includes overcoming common psychological biases like optimism bias (thinking “it won’t happen to me”) and overconfidence, and changing habitual, often insecure, behaviors into secure ones. As research confirms, “Security Awareness: The First Step in Information Security Compliance Behavior,” highlighting the direct link between informed employees and better compliance.
For us at Tech Dynamix, serving businesses in Mentor, Painesville, Cleveland, and across Northeast Ohio, we understand that robust IT security awareness isn’t just a best practice—it’s a necessity. It’s an integral part of an organization’s overall IT security strategy, helping to reduce risks, protect sensitive information, and maintain trust with clients and partners. By investing in our team’s knowledge, we minimize vulnerabilities and build a more resilient organization. This focus on awareness also complements our Compliance & Security Audits services, ensuring that your people and processes align with industry standards.
Common Cyber Threats Every Employee Must Recognize
To be effective cyber guardians, our employees need to recognize the most common and evolving cyber threats they might encounter daily. Cybercriminals are cunning, constantly adapting their tactics to exploit new technologies and human vulnerabilities.
The landscape of cyber threats is vast, but some culprits appear more frequently than others. According to the IBM Security X-Force Threat Intelligence Index 2024, the most prevalent threats often revolve around exploiting human behavior. These include:
- Social Engineering: This is perhaps the broadest and most insidious category, where attackers manipulate individuals into performing actions or divulging confidential information. It’s about psychological trickery rather than technical hacking.
- Malware: A catch-all term for malicious software, including viruses, worms, Trojans, and spyware. These programs can infect systems, steal data, disrupt operations, or hold data hostage.
- Ransomware: A particularly nasty type of malware that encrypts a victim’s files and demands a ransom payment, usually in cryptocurrency, for their release. It can paralyze an entire computer system, causing significant downtime and financial loss. You can read more about this in our article, FBI Issue New Ransomware Warning.
- Insider Threats: Not all threats come from external sources. Insider threats involve current or former employees, contractors, or business associates who have access to an organization’s systems or data and use that access to cause harm, whether intentionally or unintentionally. As we discussed in New Staff, New Security Risk, onboarding processes are critical here.
- IoT-based Attacks: With the proliferation of Internet of Things (IoT) devices, from smart office equipment to industrial sensors, each device can be a potential entry point for attackers if not properly secured.
Understanding these broad categories is the first step. Our Cybersecurity Solutions are designed to protect against these threats, but employee awareness is still key.
Identifying Phishing in IT Security Awareness
Among the various cyber threats, phishing stands out as one of the most common and effective attack vectors. It’s a type of social engineering where attackers attempt to trick individuals into divulging sensitive information or installing malware by masquerading as a trustworthy entity in electronic communication.
Phishing isn’t a single technique; it’s a family of deceptive practices:
- Standard Phishing: These are broad, untargeted attacks, often sent to thousands of email addresses, hoping a few will fall for the bait. They might impersonate well-known brands or services.
- Spear Phishing: Much more dangerous, spear phishing attacks are highly targeted. They are customized with personal information, making them appear incredibly legitimate. For example, an attacker might impersonate your CEO asking for an urgent gift card purchase or wire transfer. Gift card scams are a notorious form of spear phishing, especially during holidays. If you want to test your knowledge, why not Take the Gift Card Scams Quiz!?
- Vishing (Voice Phishing): This involves using phone calls to trick victims. Attackers might impersonate banks, government agencies, or IT support to extract information or convince you to install remote access software.
- Smishing (SMS Phishing): Similar to phishing, but delivered via text messages. These often contain malicious links or prompt you to call a fraudulent number.
- Whaling: A highly targeted spear phishing attack aimed specifically at senior executives or high-profile individuals within an organization, seeking high-value information or large financial transfers.
The key to defending against phishing is vigilance and critical thinking. Always scrutinize sender addresses, look for grammatical errors, verify links before clicking, and be wary of urgent or emotionally charged requests. Organizations like ours will never ask for sensitive information via unsolicited emails or texts. Be aware of Fake Apps Containing Malware that might be promoted through phishing.
Evolving Threats: AI and Deepfakes
The cyber threat landscape is not static; it’s a dynamic battleground where new adversaries emerge constantly. One of the most significant evolving threats we face today involves the malicious use of Artificial Intelligence (AI) and technologies like deepfakes.
Generative AI, while offering incredible benefits, can also be weaponized. Attackers are now using AI to create more convincing phishing emails, generate realistic fake websites, and even automate social engineering campaigns. This means the grammar and context of malicious messages are improving, making them harder for humans to detect. As our article, 80% of Malware Powered by AI, highlights, AI is rapidly changing the game for cybercriminals.
Deepfakes, which are AI-generated realistic images, audio, or video, pose a particularly unsettling threat. Imagine receiving a video call from your CEO, seemingly genuine, instructing you to transfer funds or reveal confidential information. This is the potential of deepfake audio and video. These sophisticated AI-powered scams blur the lines between reality and deception, making traditional “look for red flags” advice much more challenging to apply.
Our IT security awareness strategies must continuously adapt to these advancements. Employees need to be educated not just on traditional phishing indicators, but also on the subtle signs of AI-generated content, the importance of verifying requests through multiple channels, and understanding that what they see or hear might not always be real.
Building a Comprehensive Security Awareness Program
An effective IT security awareness program is not a one-time event; it’s a continuous journey designed to cultivate a security-first culture within your organization. Here in Northeast Ohio, we believe a comprehensive program involves several key components, delivered strategically and consistently.
How can organizations like ours effectively implement and deliver security awareness training? We follow a structured approach:
- Assessment and Objective Setting: First, we assess our organization’s specific risks and vulnerabilities. What data do we protect? What systems are critical? What compliance requirements must we meet? (e.g., ISO 27001, NIS2, HIPAA for healthcare clients). Based on this, we set clear, measurable objectives for what we want employees to know, understand, and do.
- Engaging Content Design: Training content must be relevant, engaging, and easy to understand. We move beyond dry lectures, incorporating real-world examples, case studies, and scenarios specific to our industry and roles.
- Diverse Delivery Methods: Different people learn in different ways. We use a mix of methods, including:
- Interactive Modules: Short, engaging online courses that allow employees to learn at their own pace.
- Phishing Simulations: This is a cornerstone. We send simulated phishing emails to test employee vigilance. If an employee falls for it, they receive immediate “point-of-failure education,” explaining what they missed and how to do better next time. These custom phishing tests can even simulate targeted spear phishing campaigns, making them incredibly realistic.
- Gamification: Turning training into a game with points, leaderboards, and rewards can significantly improve engagement and retention. Studies show that gamification improves employees’ self-efficacy and information security behaviors.
- Workshops and Webinars: Live sessions allow for questions, discussions, and deeper dives into specific topics.
- Regular Communications: Short, frequent reminders (e.g., security tips in newsletters, posters) keep security top-of-mind.
- Testing and Reinforcement: Beyond simulations, quizzes and scenario-based exercises help test understanding. Continuous reinforcement through regular updates and reminders is vital because threats evolve.
- Continuous Improvement: We constantly gather feedback, analyze metrics (like phishing click rates), and update our program to reflect new threats and lessons learned.
The NIST Guidelines for IT Security Training provide an excellent framework for building and maintaining such a program. By following these guidelines, we ensure our IT security awareness initiatives are robust and effective. Our Security services at Tech Dynamix include developing and implementing these comprehensive programs for our clients.
The Role of Leadership in IT Security Awareness
In fostering a truly security-aware culture, the role of leadership cannot be overstated. It’s not enough for IT to champion security; the message must come from the top. When leadership actively participates and prioritizes IT security awareness, it signals to every employee that cybersecurity is a fundamental business imperative, not just an IT department concern.
Managerial participation has a strong correlation with employee security awareness. Leaders set the tone, demonstrate commitment, and allocate the necessary resources. This means:
- Modeling Secure Behavior: Leaders who use strong passwords, enable MFA, and report suspicious activity themselves send a powerful message.
- Communicating Importance: Regularly discussing cybersecurity in company-wide meetings, acknowledging security efforts, and explaining the “why” behind policies helps embed security into the organizational DNA.
- Providing Resources and Support: Ensuring that employees have access to the best training, tools, and time to complete awareness modules.
- Promoting Accountability: Establishing clear expectations and consequences, but also fostering an environment where employees feel safe to report incidents or mistakes without fear of undue reprisal.
Leadership’s role is to transform compliance from a reactive exercise into a proactive, “security-first culture.” This shared commitment helps prevent incidents, but also prepares us for when new staff join, as highlighted in New Staff, New Security Risk, ensuring they integrate into a security-conscious environment from day one.
Measuring Success with Key Performance Indicators
How do we know if our IT security awareness initiatives are actually working? Measurement is critical. Without it, we’re simply guessing. Effective programs use Key Performance Indicators (KPIs) to track progress, identify areas for improvement, and demonstrate return on investment.
Key metrics we use include:
- Phishing Click Rates: This is a direct measure of how well employees are identifying and avoiding malicious emails. A declining click rate on simulated phishing emails indicates improved awareness.
- Reporting Frequency of Suspicious Activity: We want employees to report anything that looks even slightly off. An increase in legitimate reports suggests a more vigilant and engaged workforce.
- Training Completion Rates: While not a direct measure of understanding, high completion rates show engagement with the program.
- Incident Reduction: Over time, a successful awareness program should contribute to a decrease in security incidents directly attributable to human error, such as malware infections (which we’ve seen decrease by 57% in some contexts) and compromised accounts (down by 96%).
- Policy Adherence Rates: Tracking compliance with security policies, such as strong password usage or proper data handling.
Regularly analyzing these metrics, as discussed in Research on evaluating security awareness initiatives, allows us to refine our training content, tailor it to specific weaknesses, and demonstrate the tangible benefits of our awareness efforts to stakeholders.
Policy and Compliance: ISO 27001 and NIS2
For many organizations, particularly those in regulated industries in Northeast Ohio and beyond, IT security awareness is not just a good idea—it’s a legal and regulatory mandate. Frameworks like ISO 27001 and the NIS2 Directive play a significant role in shaping how we approach security awareness training.
ISO 27001: The International Standard for Information Security
ISO 27001 is the international standard for establishing, implementing, maintaining, and continuously improving an Information Security Management System (ISMS). Its focus is on systematic risk management, encompassing people, processes, and technology. Under ISO 27001, organizations must ensure that all employees and relevant stakeholders are aware of:
- Information security policies and procedures.
- Their individual roles and responsibilities in maintaining information security.
- The consequences of non-compliance.
Awareness training under ISO 27001 isn’t just a checkbox; it ensures everyone understands how to protect data, identify risks, and follow internal security controls correctly. It emphasizes the importance of secure practices like locking screens, using strong authentication, and reporting suspicious activity.
NIS2 Directive: Strengthening EU Cybersecurity Resilience
The NIS2 Directive (Network and Information Systems Security), enforced in EU countries since 2024, expands upon the original NIS Directive and sets stricter cybersecurity requirements for essential and important sectors. While primarily an EU regulation, its influence extends globally as companies operating internationally must comply. NIS2 mandates technical and organizational measures, with a strong emphasis on awareness and training. Under NIS2, individuals with access to IT systems or sensitive information are expected to:
- Understand basic cyber risks.
- Recognize and report suspicious activities.
- Practice secure password management.
- Apply preventative measures.
NIS2 also links awareness directly to incident reporting and resilience. Training ensures employees know how to report incidents quickly and through correct channels, minimizing penalties and recovery times.
Other Key Regulations (HIPAA, GDPR, PCI-DSS)
Beyond ISO 27001 and NIS2, numerous other regulations necessitate robust IT security awareness training:
- HIPAA (Health Insurance Portability and Accountability Act): For our healthcare clients in Northeast Ohio, HIPAA mandates training to protect Protected Health Information (PHI).
- GDPR (General Data Protection Regulation): This EU regulation, with global implications, requires data protection awareness, emphasizing privacy and individual rights.
- PCI-DSS (Payment Card Industry Data Security Standard): Any organization handling payment card data must provide security awareness training to ensure secure processing and storage.
We view these regulations not as burdens, but as blueprints for building trust and resilience. By aligning our awareness programs with these standards, we ensure consistency and help our employees understand the “why” behind every security practice. Our expertise in Microsoft 365 Cloud Support also ensures that cloud-based operations meet these stringent compliance requirements.
Here’s a quick comparison of how ISO 27001 and NIS2 influence awareness requirements:
| Feature | ISO 27001 | NIS2 Directive |
|---|---|---|
| Primary Focus | Establishing a comprehensive ISMS | Strengthening sector-specific cyber resilience in EU |
| Awareness Goal | Ensure understanding of policies & individual roles | Ensure understanding of basic cyber risks & reporting |
| Scope | Applicable to any organization seeking certification | Mandatory for essential & important sectors in EU |
| Key Emphasis | Risk management, policy adherence, continuous improvement | Incident reporting, supply chain security, resilience building |
| Training Requirement | Formal awareness of ISMS, roles, and responsibilities | Training on incident recognition, secure practices, reporting |
| Measurement | Part of ISMS audit & review | Effectiveness measured through incident handling, compliance |
Best Practices for an Acceptable Use Policy (AUP)
A strong IT security awareness program is incomplete without a clear and enforceable Acceptable Use Policy (AUP). An AUP is a formal document that provides guidance on the rules and guidelines for employees and other stakeholders when using the company’s IT resources. Think of it as the cybersecurity rulebook that protects your organization’s digital assets, reputation, and even its people.
Here are some best practices for creating and enforcing an effective AUP:
- Define Scope and Applicability: Clearly state who the policy applies to (all employees, contractors, guests) and what resources it covers (computers, networks, software, email, internet access, mobile devices).
- USB Drive Safety: USB drives are notorious vectors for malware. Your AUP should explicitly address their use. Best practice is often to prohibit personal USB drives and require any necessary company-issued drives to be scanned and approved by IT. Employees should be trained to never plug in unknown USBs. This is a critical discussion point in events like the SANS Cyber Threat Intelligence Summit 2025.
- Approved Software: Unauthorized software can introduce vulnerabilities or violate licensing agreements. The AUP should state that only approved, legitimate software can be installed on company devices, and outline the process for requesting new software.
- Bring Your Own Device (BYOD) Policy: With many employees using personal phones, tablets, or laptops for work, a BYOD policy is essential. It should specify:
- What types of devices are allowed.
- How personal devices can connect to the corporate network.
- Data segregation and security requirements (e.g., encryption, remote wipe capabilities).
- The organization’s right to quarantine or confiscate a personal device if it becomes a security risk.
- External Network Usage: Provide clear guidelines for using company-issued devices on external networks (e.g., public Wi-Fi). Emphasize the risks of unsecured networks and recommend using VPNs.
- Password Management and Multi-Factor Authentication (MFA): The AUP should mandate strong, unique passwords for all accounts and require the use of MFA wherever possible. MFA adds a crucial layer of security, making it much harder for attackers to gain access even if they steal a password. We’ve seen how MFA significantly reduces compromised accounts.
- Data Access and Handling: Clearly define rules for accessing, storing, and sharing sensitive data, especially concerning our article Half of Staff Have Too Much Access to Data. This should align with data classification policies.
- Consequences of Violation: Outline the disciplinary actions for violating the AUP. This provides clarity and ensures employees understand the seriousness of non-compliance.
- Regular Review and Updates: The digital landscape changes rapidly, so your AUP must be a living document, reviewed and updated annually or whenever new technologies or threats emerge.
- Integration with Training: The AUP shouldn’t just be a document; it must be integrated into your IT security awareness training, ensuring employees understand its contents and their obligations.
A well-crafted AUP, combined with consistent training, provides the necessary framework for secure and responsible technology use within your organization, protecting it from both intentional and unintentional misuse.
Frequently Asked Questions about IT Security Awareness
What is the difference between security awareness and training?
While often used interchangeably, IT security awareness and training serve distinct purposes. Awareness focuses on the “what” and aims for recognition. It’s about making employees conscious of the existence of cyber threats, the risks they pose, and the general importance of security. Think of it as a broad understanding of the cybersecurity landscape. Training, on the other hand, focuses on the “how” and aims for skill development. It provides employees with the specific knowledge and practical skills needed to perform tasks securely, such as how to identify a phishing email, properly handle sensitive data, or use new security tools. Education, the third component, digs into the “why,” fostering a deeper understanding and insight into security principles.
How often should employees receive security awareness training?
For optimal effectiveness, IT security awareness training should be an ongoing process, not a one-off event. We recommend formal training for all new employees during onboarding and at least annually for all staff. However, this should be supplemented by more frequent, shorter interventions. This can include monthly simulated phishing exercises, regular security tips via email, short educational videos, or interactive quizzes. The goal is continuous reinforcement, as threat vectors constantly evolve, and consistent reminders help keep security best practices top-of-mind.
Why is an Acceptable Use Policy (AUP) necessary?
An Acceptable Use Policy (AUP) is crucial because it clearly defines the rules and guidelines for how employees can use the organization’s IT assets and resources. It sets expectations for responsible behavior, protecting the company in several ways: it safeguards against malware and data breaches by outlining safe practices (e.g., around USB drives and software installation), prevents misuse of company resources (e.g., for non-work-related browsing), mitigates legal and compliance risks, and ultimately protects the organization’s reputation and digital infrastructure. Without a clear AUP, employees might unknowingly engage in risky behaviors, leaving the organization vulnerable.
Conclusion
In today’s interconnected world, where cyber threats are more sophisticated than ever, IT security awareness is no longer optional—it’s essential. We’ve seen how human error accounts for a staggering 95% of data breaches, making every employee a critical line of defense. By fostering a security-aware culture, educating our teams on common and evolving threats like phishing, malware, AI-powered scams, and deepfakes, and implementing robust training programs and clear policies, we empower our people to become active cyber guardians.
This journey requires continuous effort, leadership commitment, and measurable strategies. For businesses across Painesville, Mentor, Cleveland, Hudson, and throughout Northeast Ohio, building this resilience is paramount. At Tech Dynamix, we are dedicated to helping organizations like yours open up your inner cyber guardian, changing your workforce from potential vulnerabilities into your strongest defense against cyberattacks.
Ready to strengthen your organization’s cybersecurity posture? Get expert Mentor IT Support and let us help you build a comprehensive and effective IT security awareness program.




