Why Bank IT Compliance Is One of the Most Critical Challenges Facing Financial Institutions Today
Bank IT compliance is the ongoing process of aligning a financial institution’s technology systems, security controls, and operational practices with federal and state regulations — so that data is protected, risks are managed, and examiners find nothing to worry about.
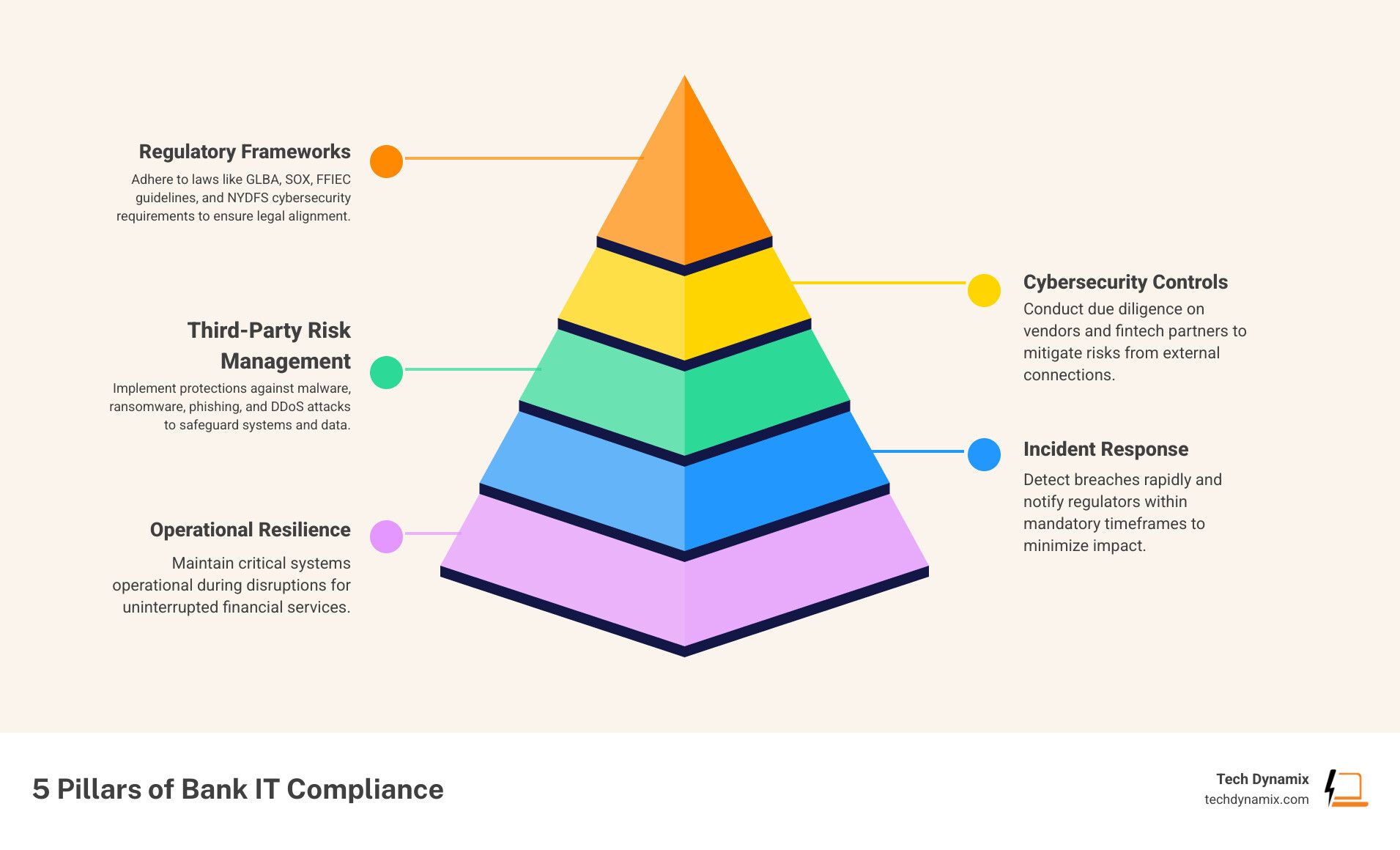
Here’s a quick snapshot of what it covers:
| Pillar | What It Means |
|---|---|
| Regulatory Frameworks | Following laws like GLBA, SOX, FFIEC guidelines, and NYDFS cybersecurity rules |
| Cybersecurity Controls | Protecting systems from malware, ransomware, phishing, and DDoS attacks |
| Third-Party Risk Management | Vetting vendors and fintech partners who touch your data or systems |
| Incident Response | Detecting breaches fast and notifying regulators within required timeframes |
| Operational Resilience | Keeping critical systems running even when something goes wrong |
The stakes are high. Non-compliance can mean millions in fines, executive liability, and lasting damage to customer trust. Under the Sarbanes-Oxley Act alone, violations can result in fines up to $25 million per incident — and officers personally face up to $5 million in fines and 20 years in prison.
And the pressure isn’t easing up. New and evolving regulations across cybersecurity, capital requirements, and operational resilience are landing faster than most compliance programs can adapt. Add in cloud complexity, AI tools, and an expanding web of fintech partnerships, and the compliance challenge grows every year.
This guide is designed to cut through the noise. Whether you’re an IT manager at a community bank or a compliance officer trying to stay ahead of your next examination, you’ll find clear, actionable guidance here.
I’m Jay Baruffa, founder of Tech Dynamix, and with over 20 years in IT infrastructure, cybersecurity, and compliance support, I’ve helped organizations across Northeast Ohio build IT environments that hold up under scrutiny — including the rigorous demands of bank IT compliance. Let’s break this down together, one piece at a time.
Essential bank it compliance terms:
- Auditing IT Security Policy Compliance
- Automated IT Security Policy Compliance Systems
- IT Security Policy Compliance
Navigating the Regulatory Maze of Bank IT Compliance
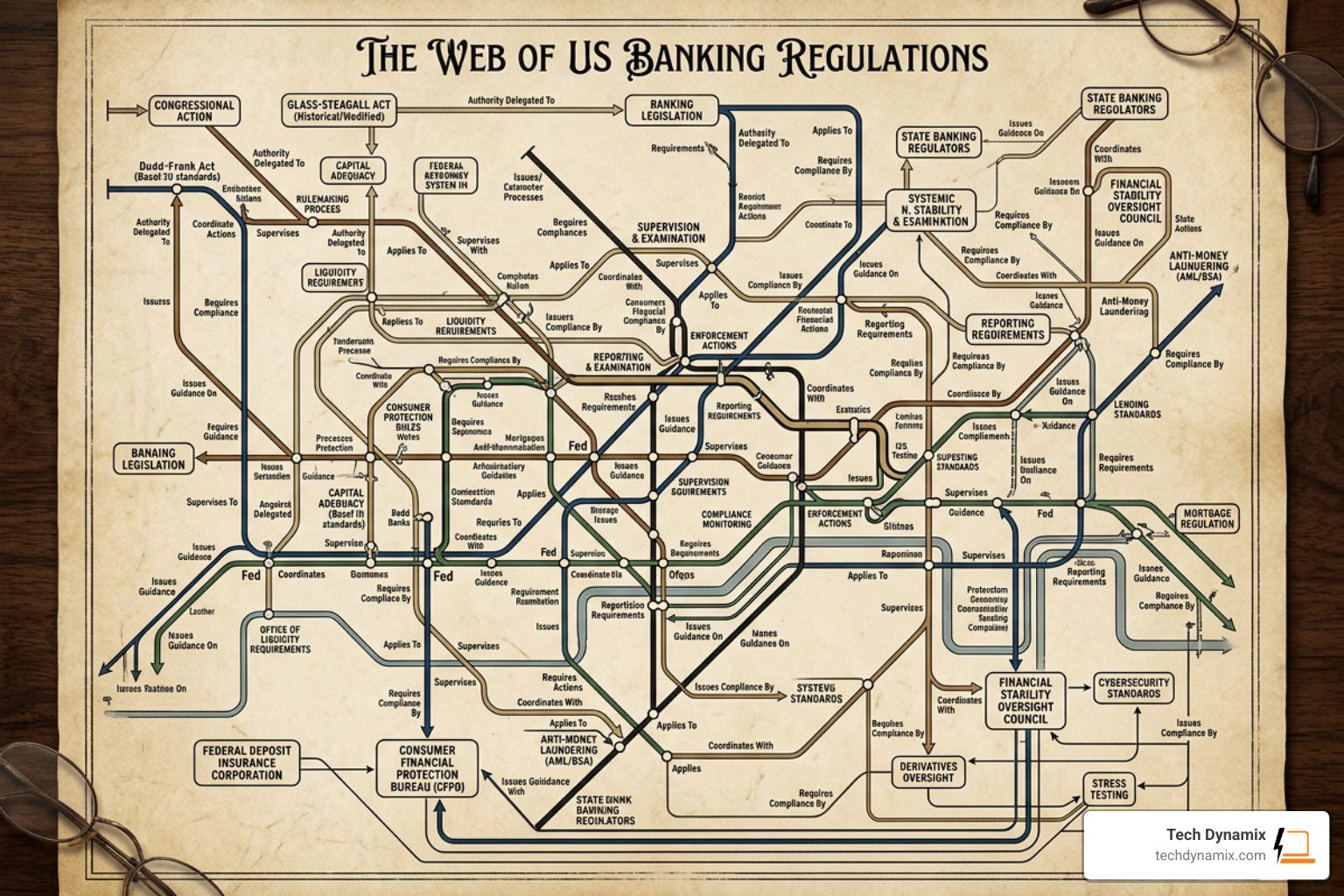
For many financial institutions in Northeast Ohio—from Mentor to Chardon—the sheer volume of regulations can feel like a labyrinth. Bank IT compliance isn’t just about one rule; it’s a collection of federal and state mandates designed to ensure the safety and soundness of the financial system.
One of the foundational pieces is the Interagency Guidelines Establishing Information Security Standards, which requires banks to implement administrative, technical, and physical safeguards to protect customer data. This isn’t a “set it and forget it” task; it requires ongoing policy management to ensure your internal controls keep pace with new threats.
Key regulations currently shaping the landscape include:
- GLBA (Gramm-Leach-Bliley Act): Instructs institutions to protect the confidentiality of nonpublic personal information. Recent amendments have tightened the runway for reporting, requiring notification to the FTC within 30 days if a breach affects 500 or more consumers.
- NYDFS 23 NYCRR 500: While specific to New York, this has become the de facto national standard for cybersecurity. Many institutions in the Greater Cleveland area use it as their baseline for access controls and security testing.
- SOX (Sarbanes-Oxley Act): Forces banks to view IT governance as a critical part of financial governance.
- Computer-Security Incident Notification Final Rule: This FDIC-enforced rule requires banks to notify their primary federal regulator within 36 hours of determining that a “notification incident” has occurred.
Key Frameworks for Global and Local Institutions
Operational resilience has moved from a buzzword to a regulatory requirement. Frameworks like DORA (Digital Operational Resilience Act) in the EU are beginning to influence how US regulators view ICT (Information and Communication Technology) risks. Even for a local bank in Lake County, these global shifts matter because they influence the compliance and security audits performed by federal examiners.
The goal is to move beyond “check-the-box” compliance and toward a model where your capital cushions and data privacy measures are integrated into your daily operations.
The Role of the FFIEC in IT Examinations
The Federal Financial Institutions Examination Council (FFIEC) provides the primary roadmap for how regulators look at your tech. Examiners use the FFIEC Information Technology (IT) Examination Handbook to evaluate risk management processes.
A critical tool in their arsenal is the InTREx Program (Information Technology Risk Examination), which helps state and federal regulators uniformly assess risks. They aren’t just looking at your firewalls; they are looking at your governance, how your board oversees IT, and whether you are using a standardized approach to cybersecurity preparedness.
Core Components of a Robust Compliance Program
Building a sustainable bank IT compliance program requires more than just good intentions; it requires a structured framework. At Tech Dynamix, we often tell our clients in the Cleveland Metro East corridor that a robust program is built on three pillars: risk assessments, control testing, and clear policies.
You should start with a compliance checklist that maps your existing controls to specific regulatory requirements. This ensures that if a regulation like the Interagency Guidelines for Unauthorized Access changes, you know exactly which controls need updating.
Operationalizing Bank IT Compliance Through Automation
The old way of managing compliance—spreadsheets and manual logs—is no longer enough. Modern banks are “operationalizing” compliance by weaving it into their daily workflows.
| Feature | Manual Compliance | Automated Compliance |
|---|---|---|
| Evidence Collection | Manual screenshots and folder filing | Automated log ingestion and timestamping |
| Alert Triage | Humans sorting through thousands of “noise” alerts | AI-assisted triage to highlight high-risk items |
| Reporting | Weeks of preparation before an exam | Real-time dashboards and instant audit trails |
| Error Rate | High due to human fatigue and data silos | Low due to standardized, repeatable workflows |
Using AI-assisted triage can significantly cut false positives in fraud monitoring, allowing your team to focus on actual threats rather than chasing ghosts. This technology routes higher-risk items to human analysts faster while reducing the noise from routine flags.
Essential Policies and Procedures
Your policies shouldn’t be static PDFs gathering digital dust. They should be operational playbooks. A core security policy must define user access rights based on the “need-to-know” principle. This means access is only granted if it’s required for a specific task, and those rights are regularly recertified.
Furthermore, your business continuity and disaster recovery plans must be tested, not just written. Examiners want to see that you have a “response program” ready to go the moment an incident is detected.
Managing Third-Party Risks and Cybersecurity Threats
Banks no longer operate in a vacuum. Between fintech partnerships and cloud service providers, your “attack surface” is much larger than your physical branch network in Willoughby or Mayfield Heights.
The Bank Service Company Act gives the FDIC authority to examine certain service providers. As a bank, you are required to notify the FDIC within 30 days of establishing a relationship with a third party that provides critical services.
Recent interagency guidance on third-party risk management emphasizes that you cannot outsource your responsibility. You must conduct deep due diligence on every vendor, ensuring their cybersecurity solutions match your institution’s risk appetite.
Strengthening Infrastructure for Bank IT Compliance
To stay compliant, your underlying IT infrastructure needs to be rock solid. This starts with endpoint detection and response (EDR), which acts as a digital shield against modern threats.
Other essential infrastructure components include:
- Multi-Factor Authentication (MFA): No longer optional; it is a baseline expectation for any system touching financial data.
- Patch Management: Vulnerabilities like “Heartbleed” or “Shellshock” proved that unpatched systems are a massive liability.
- Cloud Security: When using cloud services, you must follow FFIEC risk management principles to ensure data remains segregated and encrypted.
Protecting Against Evolving Cyber Attacks
The threat landscape is constantly shifting. Banks are currently facing a rise in destructive malware and sophisticated phishing attacks aimed at stealing employee credentials.
We recommend all Northeast Ohio financial institutions consult the FFIEC Cybersecurity Resource Guide to stay updated on ransomware-specific resources. Additionally, while cyber insurance is a valuable part of a risk management program, regulators remind us that it is not a substitute for robust internal controls.
The High Cost of Non-Compliance
Non-compliance is a “double hit” for banks. First, there is the immediate financial penalty. Under DORA, penalties can reach 2% of global annual turnover. Under SOX, as mentioned, executive accountability can include actual jail time for officers who certify inaccurate reports.
Second, there is the long-term reputational damage. In a community-focused area like Lake or Geauga County, trust is everything. A single high-profile breach or a “Needs to Improve” rating from the FDIC can lead to:
- Growth Restrictions: Regulators may block mergers or new branch openings.
- Litigation Risks: Shareholders and customers may file class-action lawsuits.
- Loss of Consumer Trust: Customers may move their deposits to institutions they perceive as more secure.
Banks that treat bank IT compliance as a continuous process rather than a quarterly scramble are the ones that thrive and maintain that vital trust.
Frequently Asked Questions about Bank IT Compliance
How do regulators like the FDIC conduct IT examinations?
Regulators use a risk-based approach, primarily through the InTREx program. They look for evidence of strong management oversight, effective technical safeguards, and a clear understanding of the institution’s risk profile. They often start by reviewing board meeting minutes to see if IT oversight is actually happening at the highest levels.
What are the notification requirements for a computer-security incident?
Under the Computer-Security Incident Notification Final Rule, banks must notify their primary federal regulator (like the FDIC) within 36 hours of determining an incident is significant enough to disrupt operations or impact the stability of the bank. You can comply by notifying your case manager or, if they are unavailable, emailing incident@fdic.gov.
When will the FFIEC Cybersecurity Assessment Tool (CAT) be sunsetted?
The FFIEC has announced that the Cybersecurity Assessment Tool will be sunsetted on August 31, 2025. Banks are encouraged to begin transitioning to other standardized approaches, such as the NIST Cybersecurity Framework, to assess their preparedness before that deadline.
Conclusion
Mastering bank IT compliance doesn’t have to mean losing your mind. By operationalizing your controls, embracing automation, and maintaining a proactive stance on cybersecurity, you can turn compliance from a burden into a competitive advantage.
At Tech Dynamix, we’ve spent over 20 years helping small and mid-size businesses across Northeast Ohio—from Painesville to Ashtabula—navigate these complex waters. We understand the local landscape and the specific pressures facing community banks and financial service providers today.
Whether you need help with cloud migration, endpoint protection, or a comprehensive Compliance & Security Audit, we are here to be your dependable technology partner. Let us help you build a secure, resilient, and fully compliant IT environment so you can focus on what you do best: serving your customers.



