What Are Cybersecurity Protection Services — and Do You Need Them?
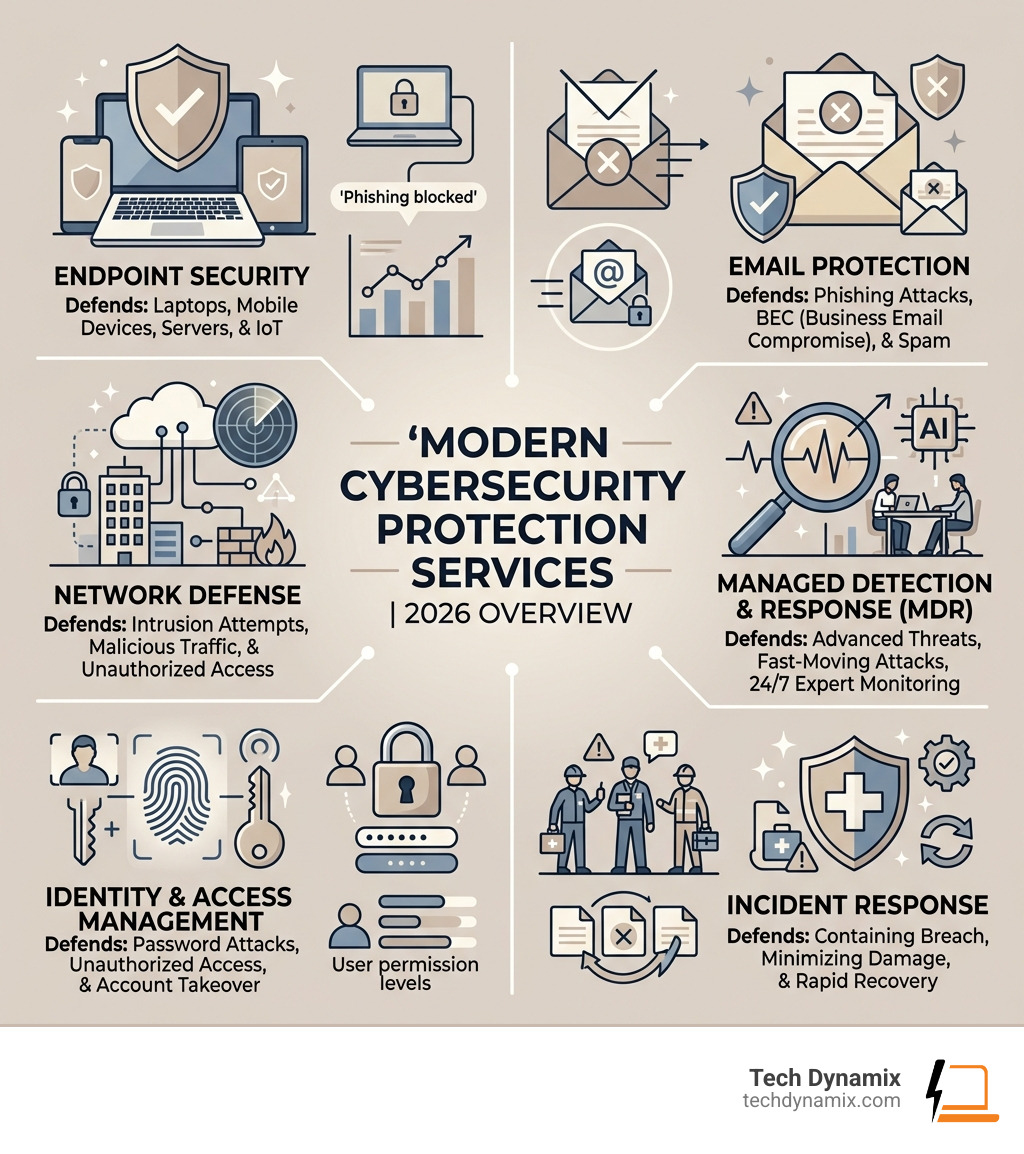
Cybersecurity protection services are managed solutions that defend your business from digital threats like ransomware, phishing, and data breaches. Here’s a quick summary of what they include:
- Endpoint security – protecting laptops, phones, and servers
- Email protection – blocking phishing, spam, and business email compromise (BEC)
- Network defense – monitoring traffic and stopping intrusions
- Managed Detection and Response (MDR) – 24/7 expert monitoring and threat response
- Identity and access management – controlling who gets into your systems
- Incident response – containing and recovering from attacks fast
If you’re a business in Northeast Ohio, these services are no longer optional. Threats are faster, smarter, and more targeted than ever before.
Cyberattacks don’t just hit big corporations. Small and mid-size businesses are frequent targets — often because attackers know they have fewer defenses. In fact, most breaches start with something as simple as a phishing email or an unpatched device.
The challenge isn’t just stopping attacks. It’s staying ahead of them around the clock, with the right tools and the right people watching your back.
That’s what modern cybersecurity protection services are designed to do.
I’m Jay Baruffa, founder of Tech Dynamix, with over 20 years of experience in IT infrastructure, network security, and compliance. I’ve spent my career helping Northeast Ohio businesses implement practical cybersecurity protection services that reduce real risk without overcomplicating things. In this guide, I’ll walk you through everything you need to know to protect your business in 2026.
Why Your Business Needs Modern Cybersecurity Protection Services

The digital landscape of 2026 is vastly different from what we saw just a few years ago. Today, adversaries operate with unprecedented stealth, often succeeding in their goals within minutes of an initial breach. For businesses from Mentor to Chardon, the question isn’t whether you have a firewall, but whether your defenses can keep up with “AI-speed” attacks.
Modern cybersecurity protection services are essential because traditional “set it and forget it” security is dead. Ransomware has evolved into a sophisticated industry, and Business Email Compromise (BEC) continues to drain bank accounts through clever social engineering. In fact, industry data shows that some platforms stop upwards of 95 million BEC attacks per year—a staggering number that highlights the scale of the threat.
It is vital to Protect Your Business from Digital Frauds by moving toward a proactive stance. This means adopting industry standards for threat management that don’t just wait for an alarm to go off but actively hunt for vulnerabilities before they are exploited.
Core Components of Cybersecurity Protection Services
Effective protection isn’t a single “magic pill.” It is a layered system of defenses. We often look at these four pillars:
- Endpoint Security: This is the frontline. Every laptop, tablet, and server is a potential entry point. Modern tools use AI to detect “fileless” malware and ransomware behaviors that traditional antivirus software would miss.
- Network Defense: Monitoring the “pipes” of your business. This involves intrusion prevention and web filtering to ensure that even if a user clicks a bad link, the malicious traffic is blocked.
- Email Protection: Since the vast majority of breaches start in the inbox, this is non-negotiable. You need systems that can identify credential theft and sophisticated phishing attempts in real-time.
- Identity Management: Ensuring that the person logging in is actually who they say they are, using Multi-Factor Authentication (MFA) and conditional access.
For smaller organizations, it’s about finding the right balance. You can read more about Cybersecurity for Small Businesses: Don’t Get Hacked to see how these components fit into a limited budget.
Evaluating the ROI of Cybersecurity Protection Services
We often hear business owners ask, “Is this worth the cost?” The answer is found in the data. Beyond preventing a catastrophic business shutdown, there are immediate financial benefits to robust security.
One of the most significant shifts in 2026 is the relationship between security and insurance. Research shows that users of comprehensive Managed Detection and Response (MDR) services claim 97.5% less on cyber insurance than those relying on basic endpoint protection alone. By proving to insurers that you have 24/7 monitoring and a prevention-first strategy, you can drastically lower your premiums.
Furthermore, these services consolidate your technology stack. Instead of paying for ten different tools that don’t talk to each other, an integrated approach improves your return on investment by reducing the “noise” your team has to manage. For a deeper dive into how this works locally, check out The Comprehensive Guide to Ohio Managed IT and Network Security.
Managed Detection and Response (MDR) vs. Traditional Security

If traditional security is a burglar alarm that rings when a window breaks, Managed Detection and Response (MDR) is a team of security guards standing inside your building, watching the cameras and patrolling the hallways 24/7.
Traditional security services often provide the tools but leave the “response” to you. If an alert pops up at 3:00 AM on a Sunday in Willoughby, who is answering it? MDR solves this by combining advanced AI-native platforms with human expertise. These experts don’t just tell you there’s a problem; they jump in to contain the threat, kick the intruder out, and fix the root cause.
This proactive hunting is what sets modern Endpoint Detection and Response: The Ultimate Cybersecurity Shield apart. It’s the difference between finding out you were robbed and stopping the thief at the door.
The Advantage of 24/7 Expert Monitoring
One of the biggest problems in IT today is “alert fatigue.” A typical business network can generate thousands of security alerts a day. Most of them are “noise”—harmless events that look suspicious.
Expert monitoring services use AI to filter out up to 85% of this noise automatically. This allows human analysts to focus on the 15% that actually matters. When a real threat is detected, the response time is measured in minutes, not hours. This rapid action is critical because, as we’ve seen in recent years, the window between an initial breach and full-scale data encryption is shrinking. You can learn how to stay ahead of these events in our guide to Mastering Computer Security Incident Management.
Incident Response Retainers and Warranties
In 2026, many cybersecurity protection services now come with added financial peace of mind. Some top-tier providers offer incident protection warranties—sometimes up to $1 million—to cover costs if a breach occurs while under their watch.
Additionally, having an incident response retainer ensures that if the worst happens, you aren’t scrambling to find a forensic analyst. You already have a team that knows your network and is contractually obligated to help you recover immediately. This kind of preparation is exactly how you Prepare Your Business for Refined Cyberthreats that are designed to bypass standard defenses.
The Role of AI and Emerging Trends in Cyber Defense
We can’t talk about 2026 without talking about AI. But we aren’t just talking about chatbots. We are seeing the rise of “Agentic AI”—systems that can think and act autonomously to defend your network.
AI-powered platforms now use deep learning to predict where an attacker might strike next based on global threat intelligence. This isn’t just science fiction; it’s a practical necessity. When 80% of malware is now powered by AI, your defense needs to be just as smart. For a look at how this is changing the game, see Unlocking Digital Fortresses: AI’s Impact on Network Security Automation.
Agentic AI and Autonomous Security Operations
Systems like IBM’s ATOM or other agentic SOC (Security Operations Center) platforms are transforming how we handle threats. These “agents” can orchestrate multiple security tasks at once—like isolating a compromised laptop, resetting a user’s password, and scanning the rest of the network for similar footprints—all in seconds.
By mapping these actions to the MITRE ATT&CK framework, these systems ensure that every possible move an adversary makes is countered. With 80% of Malware Powered by AI, having an autonomous system that can handle the volume of attacks is the only way to stay resilient.
Securing the Agentic Workspace and IoT
As we move further into 2026, the “workspace” isn’t just a desk in an office in Mayfield Heights. It’s a collection of cloud apps, mobile devices, and IoT (Internet of Things) sensors.
Protecting this “agentic workspace” means securing not just people, but the AI agents and automated processes that now handle much of our data. Whether it’s Operational Technology (OT) in a manufacturing plant in Mentor or smart medical devices in a healthcare facility, every connected “thing” needs a security profile. You can find more about this in The Complete Guide to Cloud Endpoint Security.
Choosing and Implementing the Right Security Framework
Choosing the right cybersecurity protection services can feel like ordering from a menu in a language you don’t speak. Should you go with a “Shield” package or “Complete Protection”?
The best way to decide is through a formal risk assessment. This identifies where your specific business is most vulnerable. A manufacturing firm in Ashtabula has different risks than a law firm in Cleveland. We recommend starting with a foundational framework—like the Cybersecurity Performance Goals (CPGs) outlined by CISA—and building from there. Our Compliance & Security Audits are a great starting point to see where you stand.
Compliance, Audits, and Performance Goals
Depending on your industry, you may be legally required to follow certain security standards like HIPAA (for healthcare) or GDPR (if you deal with European data). In Northeast Ohio, many businesses are also looking toward the CyberCert SMB1001 certification to prove to their partners that they are a secure choice.
Regular audits ensure that your policies aren’t just paper in a drawer, but active practices. You can use our Mastering IT Security Audits: Your Compliance Checklist to keep your team on track.
Integrated Platforms vs. Point Solutions
One of the biggest mistakes businesses make is “tool sprawl”—buying ten different products from ten different vendors. This creates a “black box” where no one knows exactly what is happening.
We advocate for integrated platforms. This gives you a “single pane of glass” view of your entire security posture.
| Feature | Point Solutions | Integrated Platforms |
|---|---|---|
| Visibility | Siloed; data is trapped in separate apps | Unified; all data correlates in one place |
| Management | Multiple logins and interfaces | Single interface for all tools |
| Response Speed | Slower; requires manual data moving | Faster; automated response across layers |
| Cost | Often higher due to multiple licenses | Usually lower through bundling and ROI |
| Complexity | High; requires expert knowledge of many tools | Lower; streamlined for efficiency |
Frequently Asked Questions about Cybersecurity Protection
What are the top free cybersecurity tools available for businesses?
While we always recommend managed cybersecurity protection services for core defense, there are excellent no-cost resources available, particularly from CISA (Cybersecurity & Infrastructure Security Agency). They offer “Cyber Hygiene” services, including vulnerability scanning and regional cybersecurity advisors who can provide guidance for critical infrastructure. However, free tools are usually “DIY”—they tell you there is a problem, but they don’t fix it for you.
How does AI-powered threat detection improve response times?
AI improves response times by removing the “friction” of manual investigation. In the past, an analyst might spend 4 to 6 hours investigating a single alert. Today, AI-driven triage can reduce that to 15 minutes or less. By the time a human looks at the incident, the AI has already gathered the context, identified the source, and often already contained the threat.
What is the difference between IT support and cybersecurity services?
This is a common point of confusion! Think of it this way: IT support is focused on availability and productivity. They make sure your email works and your printer connects. Cybersecurity is focused on adversaries and defense.
As some experts put it, a bad “bodyguard” isn’t necessarily a bad person—they just might be an IT person trying to do a security job. Cybersecurity requires a different mindset focused on how an attacker might abuse your systems. To help your team understand this shift, check out Unlock Your Inner Cyber Guardian: A Guide to IT Security Awareness.
Conclusion
In 2026, your business is only as strong as its weakest digital link. Whether you are operating in Mentor, Willoughby, or anywhere else in the Greater Cleveland area, the threats are real—but so are the solutions.
At Tech Dynamix, we believe that high-quality cybersecurity protection services should be accessible, understandable, and effective. We’ve spent over two decades serving the Northeast Ohio community, helping businesses in manufacturing, healthcare, and professional services build digital fortresses that let them focus on what they do best.
Don’t wait for a “broken window” to realize you need a better alarm. Take a proactive step today to secure your future. Get started with Cybersecurity Solutions and let us help you build a defense that never sleeps.



