Why Automated IT Security Policy Compliance Systems Matter for Your Business
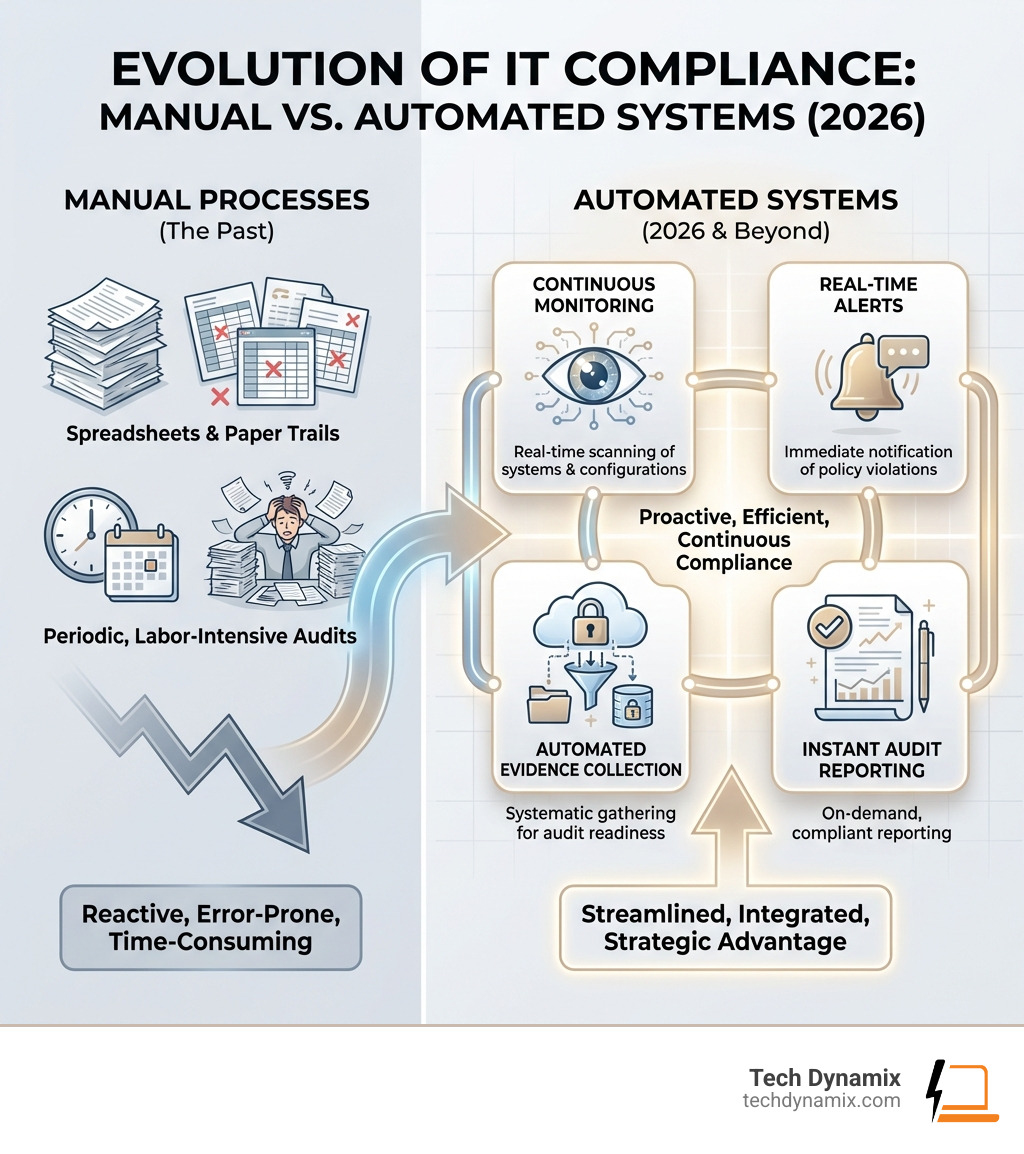
Automated IT security policy compliance systems use specialized software and continuous monitoring to enforce security policies, detect violations, and maintain regulatory adherence without constant manual intervention. These systems transform compliance from a periodic, labor-intensive process into a continuous operation integrated directly into your IT infrastructure.
Key capabilities of automated compliance systems:
- Continuous Monitoring – Real-time scanning of systems and access controls against defined policies.
- Automated Evidence Collection – Systematic gathering of compliance artifacts for audit readiness.
- Policy-as-Code – Security policies defined in code for consistent, version-controlled enforcement.
- Automated Remediation – Immediate response to violations through alerts or self-healing workflows.
- Multi-Framework Support – Simultaneous tracking across regulations like HIPAA, SOC 2, and ISO 27001.
Organizations face mounting pressure from overlapping regulatory requirements while managing limited resources. Manual processes are increasingly unsustainable – they are time-consuming, error-prone, and reactive. With cyber threats evolving rapidly, businesses need systems that keep pace without draining internal teams.
The stakes are high. Compliance failures lead to remediation costs, regulatory scrutiny, and damage to credibility. Manual audit preparation can consume hundreds of staff hours and still result in gaps. Compliance automation addresses these challenges by reducing manual effort by up to 90% and cutting costs by 30% per mandate. More importantly, it shifts security to a proactive posture, identifying violations before they become breaches.
I’m Jay Baruffa, and over my 20+ years designing IT infrastructure, I’ve seen how automated IT security policy compliance systems transform the compliance burden into a strategic advantage for Northeast Ohio businesses. At Tech Dynamix, we help organizations implement these systems to reduce risk and free up teams to focus on growth.
What are Automated IT Security Policy Compliance Systems?
Automated IT security policy compliance refers to using technology to systematically manage and enforce adherence to security standards. It moves beyond spreadsheets to intelligent systems that continuously verify that your IT environment meets predefined rules. For businesses in Northeast Ohio, this means maintaining compliance with frameworks like ISO 27001 standards or HIPAA as an ongoing, integrated process.
These systems automate repetitive tasks like data collection and reporting. They provide a real-time view of your compliance posture, flagging risks as they arise. This proactive approach ensures that clients in Mentor, Willoughby, and Painesville are continuously compliant, reducing the risk of fines.

A key aspect is “policy-as-code,” where security rules are defined using programming languages. This ensures consistency across diverse environments, from on-premise servers in Cleveland East Suburbs to cloud infrastructure in Lake County. It shifts compliance from static documents to dynamic, enforceable rules.
Core Components of Compliance Automation
Rule-Based Systems and Policy Engines: These contain the codified regulations the system enforces. Whether it is HIPAA regulations for a healthcare provider in Highland Heights or general best practices, these engines apply rules to assess configurations and access controls.
Data Monitoring and Collection: This component continuously gathers data from servers, workstations, and cloud platforms. It verifies that systems are configured correctly and that no unauthorized changes have occurred, providing an invaluable audit trail.
Automated Reporting and Dashboards: These systems generate real-time status reports and maintain audit logs. This is vital for clients undergoing Compliance & Security Audits, allowing them to demonstrate adherence to standards like ISO 27001 or Ohio HB 96 effortlessly.
Remediation and Enforcement Mechanisms: When a violation is identified, the system can trigger automated workflows, such as reconfiguring a setting or blocking a deployment. These are critical parts of our Cybersecurity Solutions.
How Automated IT Security Policy Compliance Systems Differ from Manual Methods
| Feature | Traditional Manual Compliance | Automated Compliance Systems |
|---|---|---|
| Approach | Reactive | Proactive |
| Frequency | Periodic audits | Continuous monitoring |
| Human Error | High risk of oversight | Significantly reduced |
| Resource Usage | Labor-intensive | Highly efficient |
| Consistency | Varies by individual | Standardized enforcement |
| Evidence | Manual gathering | Automated documentation |
| Cost | High operational costs | Lower operational costs |
| Agility | Slow to adapt | Rapid adaptation |
| Detection | Delayed | Real-time |
Manual compliance is reactive, often leading to situations where Half Staff Have Too Much Access to Data. Automation performs checks tirelessly and consistently. It streamlines privilege reviews and ensures that only authorized personnel can access sensitive data, allowing Northeast Ohio businesses to focus on their core operations.
The Strategic Benefits of Compliance Automation
Implementing automated IT security policy compliance systems is a strategic move that delivers significant advantages. Automation can cut compliance costs by 30% per mandate and reduce manual audit efforts by 90%. This translates into substantial savings for businesses from Lake County to Geauga County.
These systems also improve audit readiness. Instead of a frantic scramble, automated systems continuously collect evidence, making report generation a simple task. Most importantly, compliance automation leads to risk mitigation. In an era where 80% of Malware Powered by AI, proactive identification of vulnerabilities is essential. These benefits are fundamental to the IT Consulting & Advisory services we provide.
Real-Time Threat Detection and Remediation
Threats are constant and evolving. Automated systems scan your environment for deviations like configuration drift, which occurs when settings deviate from their secure state. Automated tools compare current configurations against a desired state and flag discrepancies immediately.
Beyond configuration, these systems monitor for unauthorized access and unpatched vulnerabilities. When a threat is detected, the system can initiate automated patching, reducing your attack surface in minutes. Effective incident response is also improved; systems can isolate compromised machines or revoke access instantly. This is crucial as the FBI Issue New Ransomware Warning highlights the need for swift action. While powerful, these tools still require human input for optimal performance, as noted in discussions on SLA definitions and solutions.
Streamlining Audits with Automated IT Security Policy Compliance Systems
Preparing for an audit has historically been a painstaking process. Automation turns that fear into confidence by providing automated evidence logs and audit trails. Tools gather artifacts like screenshots and access logs, ensuring documentation is current. For organizations following Ohio HB 96: A Practical Path to Compliance, this means significantly less overhead.
These systems excel at standardized reporting, providing clear overviews for auditors. This makes the process faster and more accurate. Our Managed Services clients appreciate this, as it minimizes disruption to daily operations. Automation allows businesses in Kirtland and Chardon to demonstrate their commitment to security with confidence.
Implementing Automation in Modern IT Environments
Integrating automated IT security policy compliance systems into modern environments means embedding security into the fabric of operations. For Northeast Ohio businesses embracing agile development, this involves CI/CD integration. In a DevSecOps model, compliance checks become automated quality gates that scan for vulnerabilities before code reaches production.
Infrastructure-as-code (IaC) also plays a role. When infrastructure is defined in code, automated tools can validate configurations against security baselines before resources are provisioned. Tools like Open Policy Agent (OPA) documentation allow policy to be enforced across the entire IT stack. Furthermore, integrating zero trust principles ensures that every action adheres to the principle of least privilege.
Overcoming Implementation Challenges
Implementing these systems can be complex. One challenge is tool integration, as modern environments use diverse platforms. The solution lies in prioritizing API-first strategies and expanding incrementally. Another hurdle is managing false positives, which requires careful tuning of rules and risk-based prioritization.
We also encounter technical debt and legacy systems. Older infrastructure may not integrate easily, requiring strategic roadmaps for modernization. This addresses risks like New Staff, New Security Risk, where inconsistent configurations can be problematic. Finally, change management is crucial; teams need training to focus on strategic tasks rather than manual work. This strengthens security against new threats, such as those targeted by Microsoft Edge Scam Protection.
The Role of AI and Future Trends in Compliance
AI and machine learning are enabling more sophisticated risk assessment. These systems can analyze historical data to predict potential compliance risks. This is relevant as we see advancements in Demystifying AI Agents in SecOps, where intelligent agents improve efficiency.
Future trends include:
- Agentic AI: Systems that autonomously remediate compliance issues.
- Hyper-Personalized Compliance: Strategies custom to an organization’s unique risk profile.
- Predictive Analytics: Forecasting challenges based on regulatory changes.
- Continuous Adaptive Compliance: Systems that adjust policies in real-time based on the threat landscape.
For clients seeking certifications like the Why CyberCert SMB1001 Bronze Certification Matters, AI will be crucial for future-proofing data protection strategies.
Frequently Asked Questions about Compliance Automation
Can automation replace human oversight entirely?
Not entirely. We advocate for a hybrid approach where automation handles repetitive tasks, and human experts provide strategic direction. Humans are essential for interpreting complex regulations, making strategic decisions, addressing edge cases, and interacting with auditors. Automation is a powerful enabler that frees your team to focus on higher-level security aspects.
What are the cost implications and ROI of these systems?
Investing in automated IT security policy compliance systems offers a significant ROI through:
- Direct Cost Reduction: Cutting compliance costs by 30% per mandate by minimizing manual tasks.
- Reduced Fines: Lowering the risk of non-compliance and associated legal repercussions.
- Audit Efficiency: Making audits faster and less disruptive, which can reduce audit fees.
- Improved Security: Reducing the risk of costly data breaches.
- Resource Optimization: Allowing IT staff to focus on strategic Security projects.
How does automation handle rapid regulatory changes?
The key lies in policy-as-code. When policies are defined as code, they can be updated, tested, and deployed across the environment quickly. Many tools receive dynamic updates from vendors reflecting the latest changes. This agility is a stark contrast to manual methods, which can take months to update, leaving businesses in Northeast Ohio vulnerable during transitions.
Conclusion
Automated IT security policy compliance systems are a necessity for businesses in Northeast Ohio, from Mentor and Willoughby to Painesville Township. These systems transform compliance from a labor-intensive burden into a proactive, continuously enforced operation. By leveraging rule-based engines and real-time monitoring, organizations achieve higher efficiency and accuracy.
The strategic benefits include cost reductions, improved audit readiness, and robust risk mitigation. Integrating automation into modern environments ensures that security is built-in from the start. While challenges like tool integration exist, they are surmountable with expert guidance. The future of compliance, driven by AI, promises even more adaptive solutions.
At Tech Dynamix, we provide high-quality IT consulting and managed services to small and mid-size businesses across Northeast Ohio. With over 20 years of experience, we help you harness the power of automation to improve resilience and reduce risk. Don’t let regulatory complexity leave you vulnerable.
Streamline your compliance with Tech Dynamix Compliance & Security Audits



