Why Cybersecurity Services Matter More Than Ever
Cybersecurity services are professional solutions designed to protect your organization’s digital assets, data, and networks from evolving threats like ransomware, supply chain attacks, and data breaches. Here’s what they typically include:
Core Cybersecurity Services:
- Managed Detection and Response (MDR) – 24/7 monitoring and threat response
- Security Operations Center (SOC) – Continuous surveillance and incident management
- Penetration Testing – Ethical hacking to find vulnerabilities before attackers do
- Compliance Support – Help meeting standards like GDPR, ISO 27001, and PCI DSS
- Identity and Access Management (IAM) – Control who accesses what in your systems
- Endpoint Security – Protect devices from malware and unauthorized access
- Incident Response – Fast recovery when breaches occur
The business landscape has changed dramatically. As one cybersecurity leader put it: “Tech-driven transformation is now perpetual business-as-usual for organisations instead of a one-time hit.” That constant change means cybersecurity can’t be an afterthought—it needs to be at the heart of everything you do.
The stakes are high. Cyber criminals can find your business anywhere, and attacks happen faster and hit harder than ever before. Without proper protection, a single breach can threaten your reputation, operations, and even your ability to stay in business.
But here’s the good news: you don’t need to become a security expert yourself. Modern cybersecurity services combine advanced technology, expert knowledge, and continuous monitoring to keep you protected while you focus on running your business.
I’m Jay Baruffa, and over my 20+ years working with IT systems and infrastructure, I’ve seen how cybersecurity services have evolved from basic firewalls to comprehensive protection strategies that include threat intelligence, compliance management, and rapid incident response. At Tech Dynamix, we’ve built our approach around making these complex solutions simple and accessible for businesses across Northeast Ohio.
Core Types of Cybersecurity Services for Modern Organizations
In the past, you might have thought a simple antivirus program was enough. Today, the “attack surface”—the sum of all the different places a hacker could try to enter your network—is much larger. Because we use more mobile devices, cloud apps, and remote connections than ever, our cybersecurity services have had to become more specialized.
Endpoint Security and Network Protection
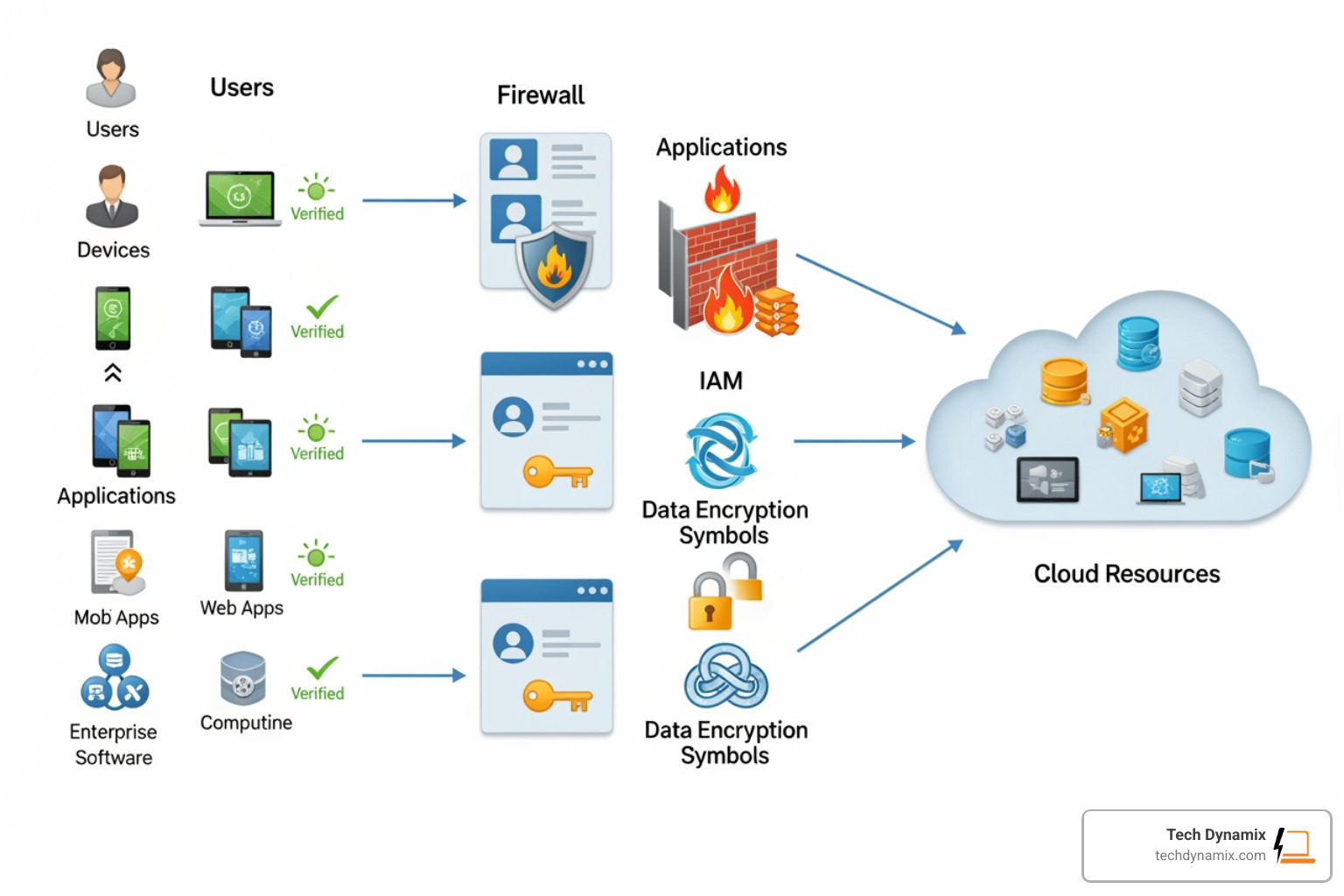
Your “endpoints” are the laptops, smartphones, and tablets your team uses every day. These are often the first line of attack. Modern endpoint security doesn’t just look for viruses; it looks for suspicious behavior. At Tech Dynamix, we focus on cybersecurity for small businesses to ensure these devices don’t become an open door for hackers. This is paired with network protection, which involves firewalls and intrusion prevention systems that act like a digital security guard for your entire office.
Identity and Access Management (IAM)
Who has the keys to your digital kingdom? IAM ensures that only the right people have access to specific data. This includes using Multi-Factor Authentication (MFA) and Single Sign-On (SSO). It sounds simple, but as we’ve noted before, half of staff have too much access to data, which creates a massive internal risk. IAM helps us lock down those permissions.
Cloud Security, Zero Trust, and SASE
As businesses in Mentor and Cleveland move to the cloud, security has to move with them. We provide managed security services that integrate Zero Trust—a philosophy where the network trusts no one by default, even if they are “inside” the office. This is often delivered through SASE (Secure Access Service Edge), which combines network security and wide-area networking into a single cloud-delivered service.
Proactive Risk Mitigation: Testing and Vulnerability Management
Waiting for an alarm to go off is a dangerous way to handle security. Instead, we use proactive cybersecurity services to find the holes before the “bad guys” do.
Penetration Testing and Ethical Hacking
Think of this as a “fire drill” for your security. An ethical hacker tries to break into your system using the same tools as a criminal. This reveals exactly where your defenses are weak. These tests are vital for understanding your real-world risk tolerance.
Vulnerability Assessments
While a penetration test is a deep dive, a vulnerability assessment is a broad scan of your entire environment. It identifies missing software updates or “bugs” that need fixing. This is especially important now that 80% of malware is powered by AI, making attacks faster and more frequent.
Security Design and Automation
We don’t just find problems; we design systems to prevent them. By unlocking digital fortresses through network security automation, we can help your systems automatically block threats the moment they are detected. For those looking for a starting point, CISA offers no-cost security tools that can provide basic scans and resources.
Managed Detection and Response (MDR) and Security Operations
If a hacker strikes at 2:00 AM on a Sunday, will your IT team be awake to stop them? This is where Managed Detection and Response (MDR) comes in. MDR is a 24/7 service that doesn’t just watch for threats—it takes action to stop them.
| Feature | SIEM | EDR | XDR |
|---|---|---|---|
| Focus | Log collection and analysis | Individual device (endpoint) security | Integrated security across cloud, network, and devices |
| Best For | Compliance and historical data | Stopping malware on laptops/servers | Comprehensive, automated threat hunting |
| Response | Alerts your team to look | Can isolate a single device | Can block threats across the whole network |
The Role of a Security Operations Center (SOC) in Cybersecurity Services
A SOC is the “mission control” for your security. It’s a facility staffed by experts who monitor your network 24/7. They use threat intelligence to stay updated on the latest ransomware warnings and trends, ensuring that if a supply chain attack or a new virus emerges, they are ready. Our accredited SOC services provide the continuous monitoring and incident escalation that small businesses in Northeast Ohio need to stay resilient.
Comparing MDR and EDR within Cybersecurity Services
While EDR (Endpoint Detection and Response) focuses on your devices, MDR is the human service that manages those tools. MDR provides proactive hunting—searching for hackers who might be hiding silently in your network. When a threat like a fake app containing malware is detected, the MDR team provides rapid containment to ensure it doesn’t spread.
Achieving Compliance and Regulatory Standards
For many of our clients in healthcare, finance, and government, cybersecurity services aren’t just a good idea—they are a legal requirement. Compliance means proving to an auditor that you are protecting data according to specific rules.
- GDPR: Essential if you handle data for anyone in the EU.
- ISO 27001: The global gold standard for information security management.
- CMMC: If you are a defense contractor in Lake or Cuyahoga County, you must meet CMMC requirements to keep your contracts. We provide deep expertise in CMMC certification to help you navigate these complex rules.
- PCI DSS: Required for anyone who processes credit card payments.
- Ohio HB 96: This is a big one for our local partners. Ohio HB 96 provides a practical path to compliance for cities, counties, and school districts, offering legal “safe harbor” if they follow recognized security frameworks.
Our compliance and security audits ensure you are audit-ready, maintaining data sovereignty and meeting all local and federal regulations.
Frequently Asked Questions about Cybersecurity Services
How do SMBs access affordable cybersecurity?
Many small businesses think they can’t afford enterprise-grade protection. However, by using managed IT, you can access scalable solutions that fit your budget. We often recommend the NCSC Cyber Action Toolkit for a free initial assessment. Additionally, certifications like the CyberCert SMB1001 show that you take security seriously without breaking the bank.
What is the role of employee training?
You can have the best firewall in the world, but if an employee clicks a bad link, the “gates” are open. We know that new staff often equal new security risks, so security awareness training is vital. This includes phishing simulations to teach your team how to spot scams.
Why are industry accreditations important?
When you hire a company for cybersecurity services, you need to know they actually know what they’re doing. Accreditations provide technical assurance that the provider follows industry standards for penetration testing and data handling. You can learn more about what to look for in our accredited cybersecurity company details.
Conclusion
At Tech Dynamix, we understand that for businesses in Mentor, Willoughby, and across the Greater Cleveland Area, technology should be an engine for growth, not a source of constant worry. Effective cybersecurity services provide the operational resilience you need to embrace digital transformation with confidence.
Whether you are looking to meet CMMC standards, protect your manufacturing plant from ransomware, or simply ensure your healthcare practice is HIPAA compliant, we provide tailored strategies aligned with your specific business needs.
Don’t wait for a breach to rethink your security. Secure your business with our cybersecurity solutions today and get the peace of mind that comes from having a local, expert team watching your back 24/7.



